Setting up a web app pentesting lab
The Broken Web Application (BWA) is an OWASP project that provides a self-contained VM complete with a variety of applications with known vulnerabilities. The applications within this VM enable students to learn about web application security, practice and observe web attacks, and make use of penetration tools such as Burp Suite.
To follow the recipes shown in this book, we will utilize OWASP’s BWA VM. At the time of writing this book, the OWASP BWA VM can be downloaded from https://sourceforge.net/projects/owaspbwa/files/.
Getting ready
We will download the OWASP BWA VM along with supportive tools to create our web app pentesting lab.
Software tool requirements
To complete this recipe, you will need the following:
- Oracle VirtualBox (https://www.virtualbox.org/wiki/Downloads): Choose an executable specific to your platform
- Mozilla Firefox browser (https://www.mozilla.org/en-US/firefox/new/)
- 7-Zip file archiver (https://www.7-zip.org/download.html)
- OWASP BWA VM (https://sourceforge.net/projects/owaspbwa/files/)
- Burp Proxy Community or Professional (https://portswigger.net/burp/)
- Oracle Java (https://www.oracle.com/java/technologies/downloads/)
How to do it...
For this recipe, you will need to download the OWASP BWA VM and install it by performing the following steps:
- Click Download Latest Version after clicking the OWASP BWA VM link provided earlier and unzip the
OWASP_Broken_Web_Apps_VM_1.2.7zfile. - You will be presented with a listing of several files, as follows:
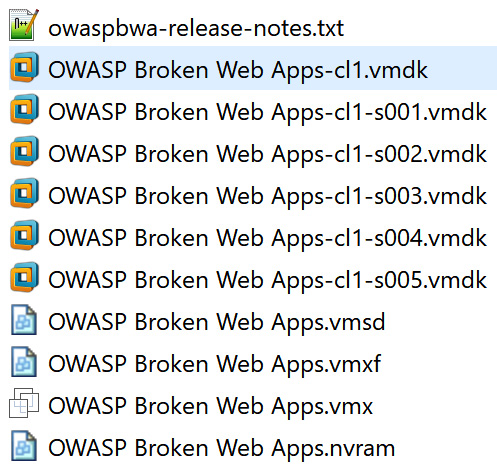
Figure 1.4 – File listing after unzipping OWASP_Broken_Web_Apps_VM_1.2.7z
- All file extensions shown indicate that the VM can be imported into Oracle VirtualBox or VMware Player/Workstation. To set up the web application pentesting lab for this book, we will use Oracle VirtualBox.
- Make a note of the
OWASP Broken Web Apps-cl1.vmdkfile. Open VirtualBox Manager (that is, the Oracle VM VirtualBox program). - Within the VirtualBox Manager screen, select Machine | New from the top menu and type a name for the machine – for example,
OWASP BWA. - Set Type to Linux and Version to Ubuntu (64-bit), and then click Next, as follows:
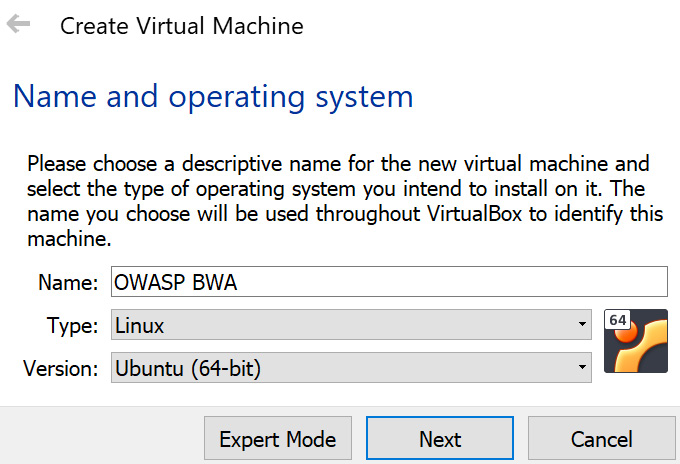
Figure 1.5 – Create Virtual Machine
- The next screen allows you to adjust the RAM or leave it as-is. Click Next.
- On the next screen, choose Use an existing virtual hard disk file.
- Use the folder icon on the right to select the
OWASP Broken Web Apps-cl1.vmdkfile from the extracted list and click Create, as follows:
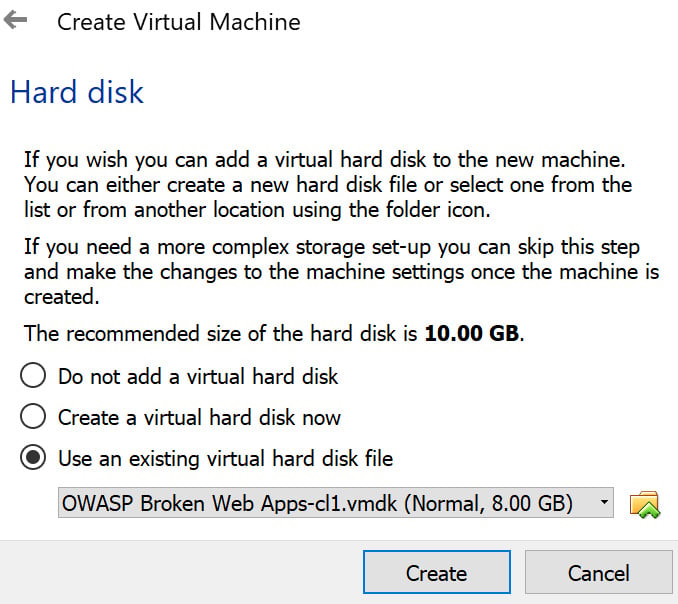
Figure 1.6 – Hard disk allocation
- Your VM will have been loaded into VirtualBox Manager. Let’s make some minor adjustments. Highlight the OWASP BWA entry and select Settings from the top menu.
- Select the Network section in the left-hand pane and change Attached to: to Host-only Adapter. Click OK:
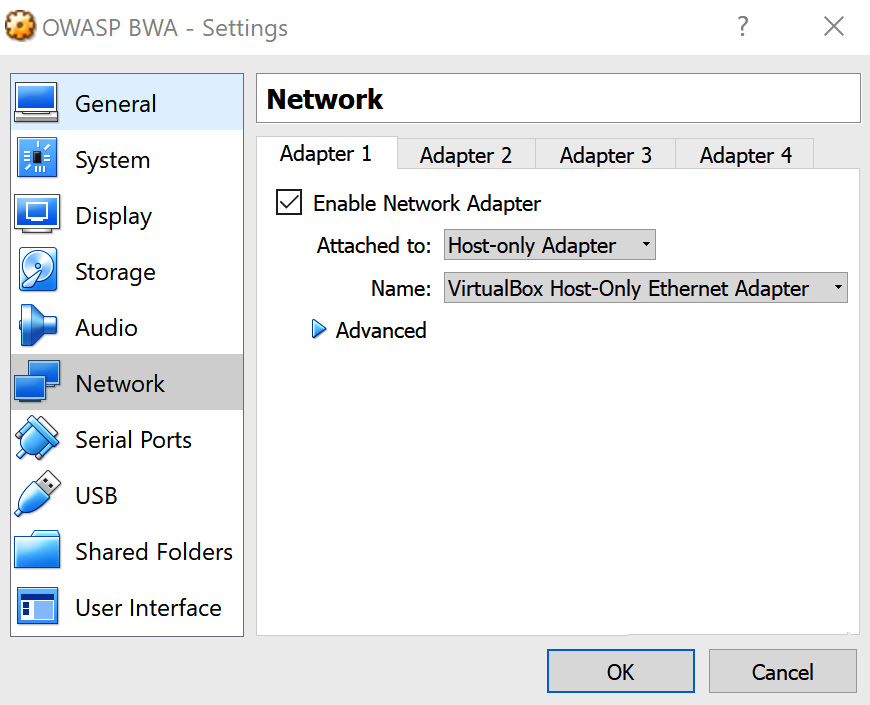
Figure 1.7 – Network adapter settings
- Now, let’s start the VM. Right-click and then choose Start | Normal Start:
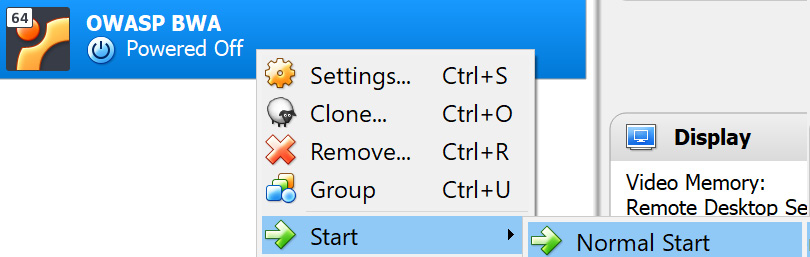
Figure 1.8 – Starting the VM
- Wait until the Linux system is fully booted, which may take a few minutes. After the booting process is complete, you should see the following screen. Note that the IP address shown will be different for your machine:
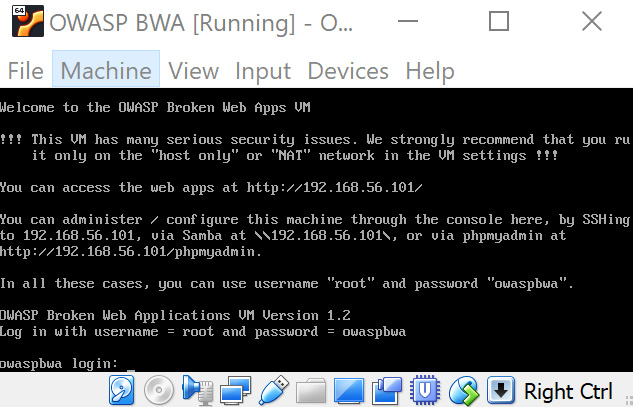
Figure 1.9 – Your assigned IP address for the VM
- The information presented on this screen identifies the URL where you can access vulnerable web applications running on the VM. For example, in the previous screenshot, the URL is
http://192.168.56.101/. You will be given a prompt to administer the VM, but it is not necessary to log in at this time. - Open the Firefox browser on your host system, not in the VM. Using the Firefox browser on your host machine, enter the URL provided (for example,
http://192.168.56.101/), where the IP address is specific to your machine. - In your browser, you will be presented with an index page containing links to vulnerable web applications. These applications will be used as targets throughout this book:

Figure 1.10 – Splash page of the VM
How it works…
Leveraging a customized VM created by OWASP, we can quickly set up a web app pentesting lab containing purposefully vulnerable applications that we can use as legal targets for our exercises throughout this book.
































































