Incident response life cycle (hunting as proactive detection)
There are numerous different incident response life cycles that can be found through a short search across the internet. To keep things simple, any time this book references the incident response life cycle, it will be alluding to the one found in the following diagram:
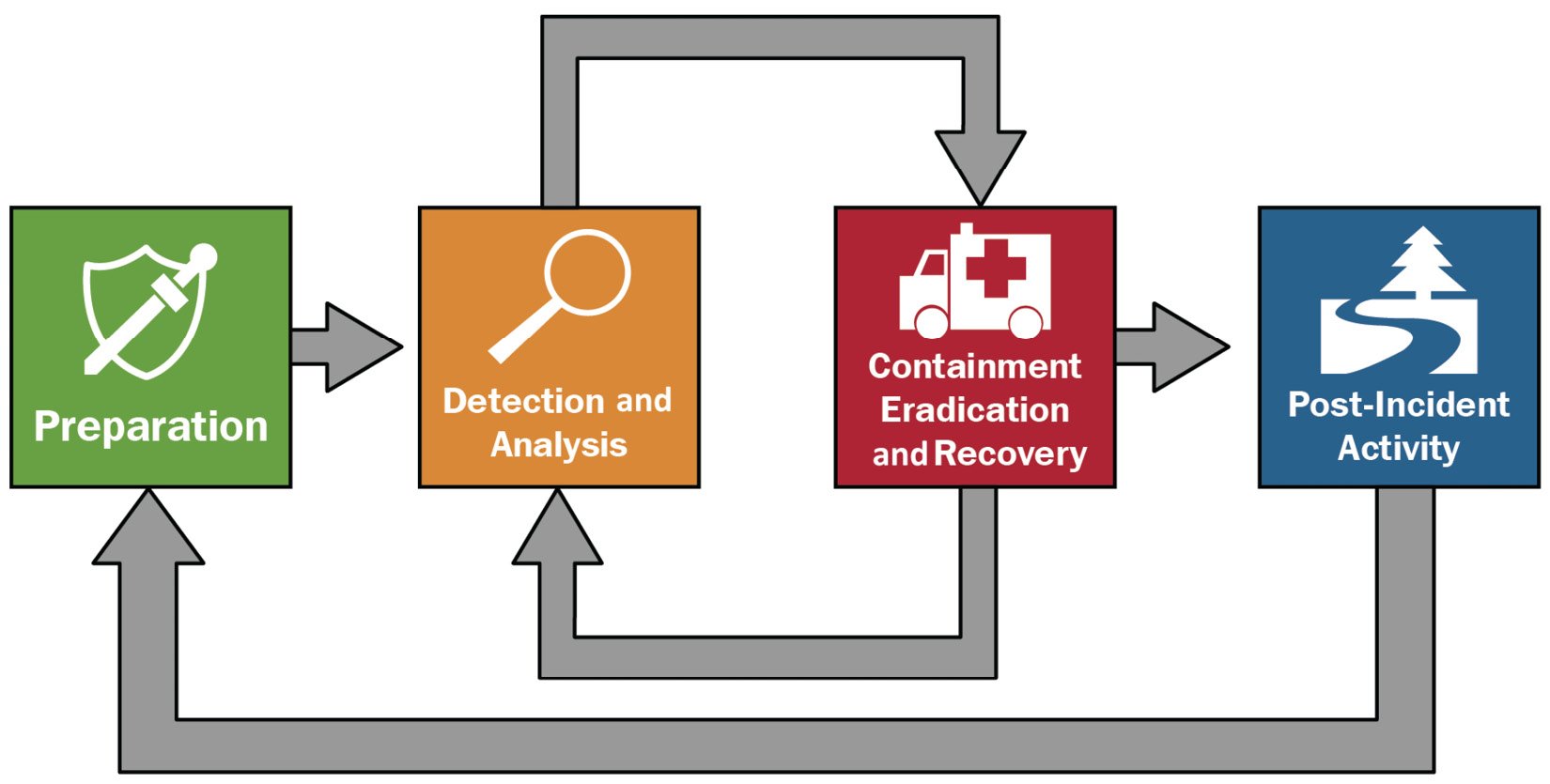
Figure 1.1 – NIST SP 800-61r2 incident response life cycle
The cycle always starts out with a Preparation phase, regardless of whether it is done purposefully or not. The following two steps, Detection and Analysis and Containment, Eradication, and Recovery, are cycled between as new information is identified and cases expanded. Once everything has been recovered, there will be a Post-Incident Activity phase in which a review of the events can be conducted without any pressure to recover. Good practices can be encouraged and bad practices pruned. Let's take a closer look at each of these phases.
Preparation
Plan for incidents, document assets and actions, architect for secure solutions, baseline the network, and so on. This is where an organization will prepare for the employment of cybersecurity resources. Even if they completely outsource their risk and response to another entity, the owning organization will take part in this phase. There will always be a level of preparation completed; sometimes it just happens to be that the organization decides not to prepare at all.
Some such examples of activities found within this phase include measuring baseline network activity, reviewing and documenting standard processes, and stress testing response scenarios. For example, if a virus was found on a network, how would the administrators respond? Preparation would allow them to understand the best course of action in relation to the business priorities that would allow them to minimize risk to the organization and its priorities. With inadequate preparation, the next few phases will be purely responsive with a higher level of risk to the organization.
Detection and analysis
During this phase, the organization will identify what is perceived to be benign and what is potentially malicious. This includes detection of activity, analysis of that activity, and a full-scope investigation as needed to determine the root cause and scope of the event. Cyber threat hunting is only a part of this step. The threat hunting step can be iterated over and over before a vulnerability or incident is identified that requires containment, eradication, and recovery. It does well to understand that this phase does not have to be completed by the organization that owns the network. Detection of an event can come from any number of places, including government agencies, hacktivists, underground hacking forums, and news sites.
Some examples of activities found within this phase include monitoring antivirus and firewall lows, comparison of baseline network activity against current network activity, and threat hunting. Anything that brings a particular activity to the focus of a cyber defender could fall under this phase of the cycle.
Containment, eradication, and recovery
Slow down, remove, and recover from the realization of a vulnerability that was exploited. The overarching goal is for the enterprise and organization to leave this phase operating at whatever the previously defined concept of normal was. This phase is largely dependent upon the planning that was conducted during the first phase because it will outline the methods in which the recovery activities are executed. If these actions were not properly planned or completed poorly during the first phase, then this phase will be an extreme struggle in a time of already heightened stress. One item of note is that it is expected for the middle phases of this life cycle to loop back and forth as new information is identified and additional pieces of the puzzle on the adversary are put into place. There will be a clear stopping point: all key data points have been identified and recovered from or all funds for the incident have been expended.
This phase is dependent upon the thoroughness of the previous phase. Some example activities include the locking of accounts, the implementation of additional firewall rules, and having users retake cybersecurity awareness training. Any activity that helps reset the network back to the previous baseline without the offending action could be included in this phase. Many of the organizational-level activities that occur in this phase will be outside the scope of a traditional threat hunting team.
Post-incident activity
This phase is intended to ensure that the risk is removed and the vulnerability is not exploited again. Within this phase, the organization will attempt to learn from the incident that occurred and the recovery that took place. Unfortunately, at this point, the organization and defenders are normally tired of the whole event and want to be done. This phase is the most overlooked and underaccomplished of the four phases, which explains why many organizations are compromised in the same way repeatedly. Everyone must learn from the correct and incorrect things that occurred in order to not repeat the mistakes of the past. Failure to do so is inviting those same things to happen again to the detriment of the organization.
Some examples of activities that take place include the incident response debrief for an intrusion and the reviewing of patching policies. Many of the organizational-level activities that occur in this phase will be outside the scope of a traditional threat hunting team.
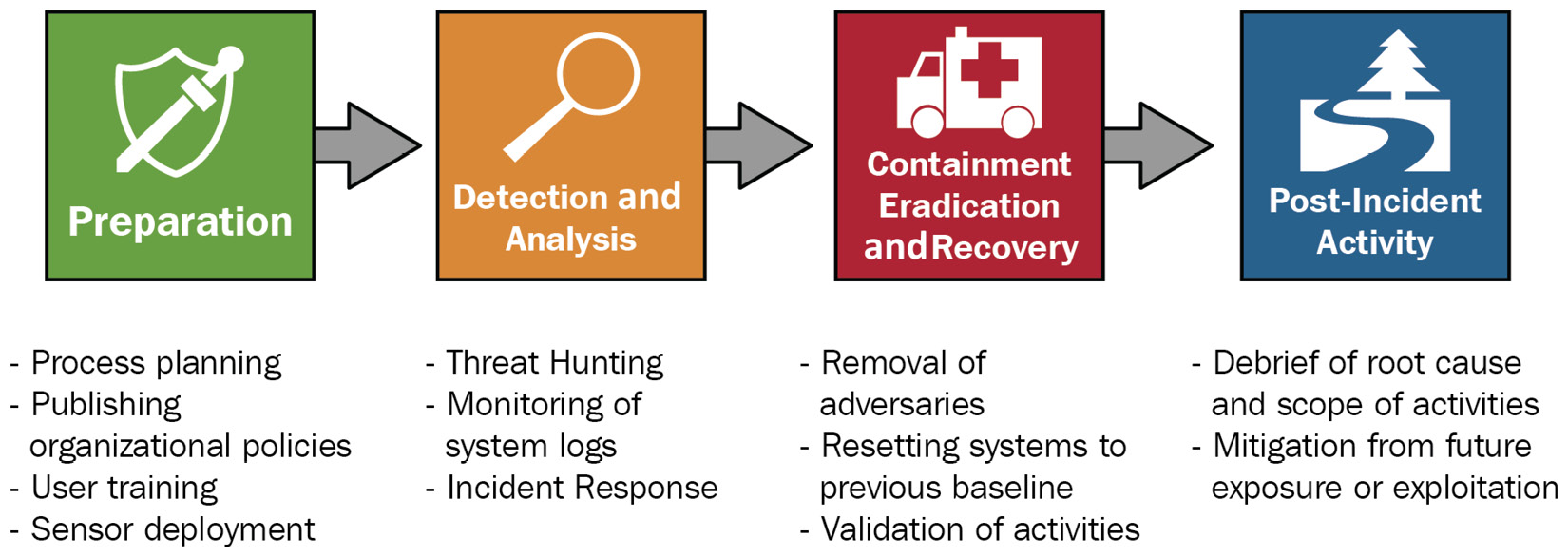
Figure 1.2 – Sample activities that occur in each phase
There are many activities that can occur in each phase of the incident response life cycle with stakeholders taking part in some or all of the phases. The most important takeaway to have when working through this cycle is to understand which phase you are in and what you are intending to accomplish. Follow the process and employ the correct teams and personnel as needed. If an adversary is just discovered, do not jump ahead and attempt to begin the removal of any artifacts that are found.