What you’ll need to play the EoP game
To get started, you’re going to need a couple of things, depending on how you intend to play the game. Firstly, you are going to need a detailed architecture diagram showing the data flows and preferably the trust boundaries.

Figure 1.1: Diagram showing data flows and trust boundaries
What are the trust boundaries? They are the boundaries where data passes from one level of trust to another, for example, user input, which is untrusted data and data that has then been sanitized (had any invalid characters or commands removed), or data coming from the internet through the firewall and onto your network. In both cases, the second example is something you should be more willing to trust.
If you’re going to be playing remotely, read the next section.
Having the cards either digitally or physically is going to be a help, so reading the section entitled The cards will point you to where you can download them digitally or purchase them online.
Remote threat modeling
If you’re doing remote threat modeling exercises and you have a Miro account, you might find my Threat Modeling with EoP Miro template handy: https://miro.com/miroverse/threat-modeling-with-eop/.
The board contains instructions on how to get set up and a working example showing how the Miro board was intended to be used.
To deal with the cards for the remote exercise, Agile Stationery has kindly created a card-dealing web application:
https://croupier.agilestationery.co.uk/
Here, you can download TNG Technology Consulting GmbH’s online multiplayer version of the threat modeling card games that you can host on-premises, such as EoP, OWASP Cornucopia, and Cumulus:
https://github.com/tng/elevation-of-privilege
The cards
The following resources are where you can get your hands on a copy of the EoP cards or those of one of its extensions required to play the game, either virtually or physically:
- Here’s Adam Shostack’s GitHub repository for EoP where you can download the cards: https://github.com/adamshostack/eop
- Mark Vinkovits Privacy Extension can be found here: https://logmeincdn.azureedge.net/legal/gdpr-v2/eop-cards-ready-to-print.pdf
- F-Secure Corporation’s Elevation of Privacy (T.R.I.M.) Extension can be found here: https://github.com/WithSecureOpenSource/elevation-of-privacye
- You can buy physical copies of the cards from Agile Stationery as well: https://agilestationery.com/collections/cybersecurity-games
Alternative games
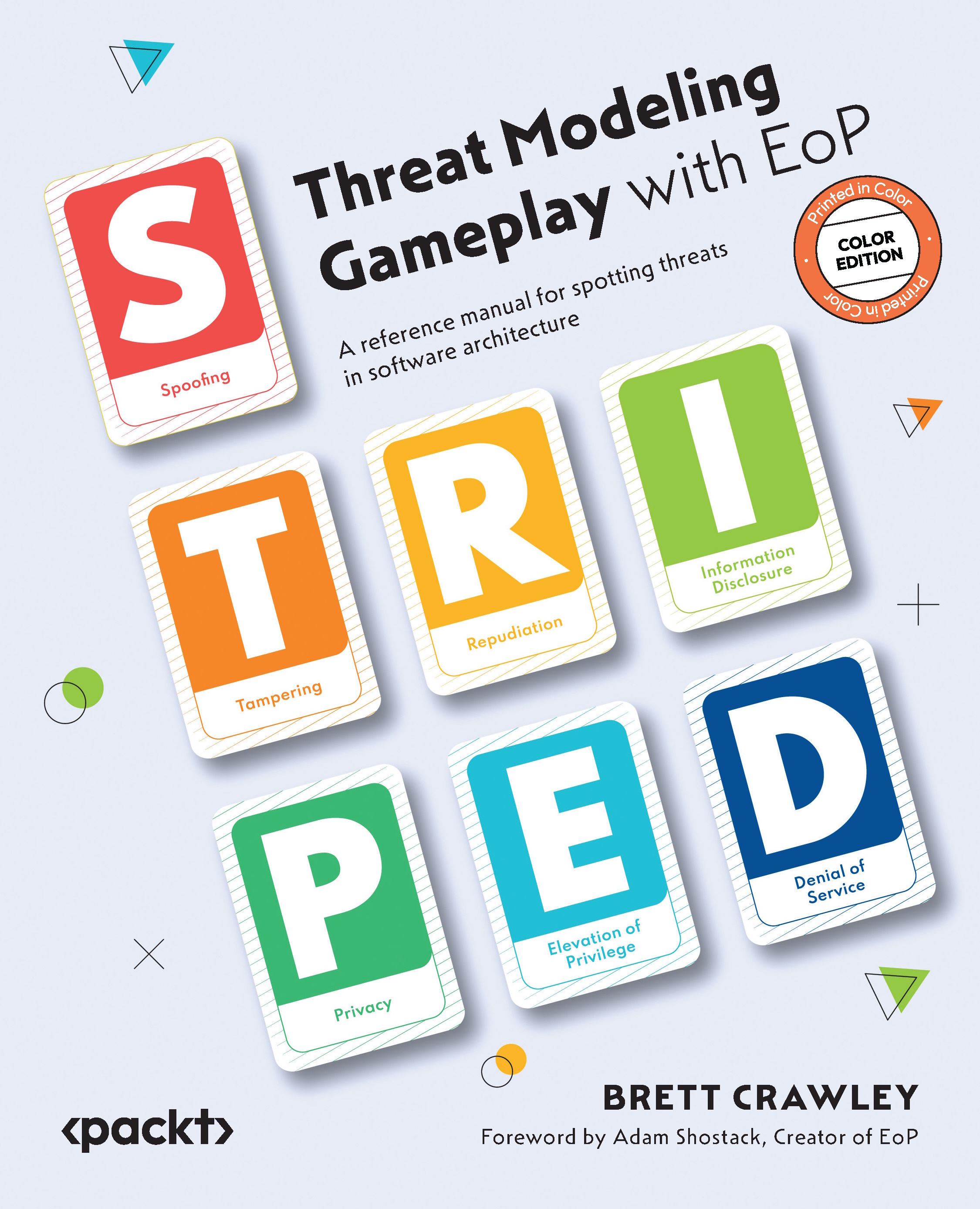
Two other threat modeling games that are quite similar to EoP in how you use them are Cornucopia from OWASP and Cumulus from TNG Technology. Many of the examples from this book will be applicable to cards in these games. Cornucopia is specifically designed for e-commerce applications and there are more threat categories, however, it doesn’t map directly to STRIDE (which stands for the following threat categories: spoofing, tampering, repudiation, information disclosure, and EoP) if you have chosen to use this methodology. Cumulus, as the name suggests, is aimed at threat modeling cloud solutions. You can download these two games at the following links:
- OWASP Cornucopia: https://owasp.org/www-project-cornucopia/#div-cards
- TNG Technology Consulting GmbH’s Cumulus Cloud Threat Modeling Cards: https://github.com/TNG/cumulus
Now that we have the resources we need to play the game, let’s see who you should invite to play this game