Summary
You’ve now covered the threat types described on the cards from the Elevation of Privilege suit in the Elevation of Privilege card deck. This, for obvious reasons, is also the trump suit for the game, not only for its name but also for the gravity of the risks these threats pose. These threats detailed flaws relating to supply chain attacks, insecure cloud solutions, containers and virtualization, poor documentation, XSS, and different forms of injection.
You should now understand the following:
- The need to have a vendor selection process and look at their track history
- The need to use MFA
- When to choose dedicated hardware
- The need to document your APIs thoroughly
- The need to verify assumptions you are making when using third-party APIs
- The need to validate and sanitize input and output as well as to encode output
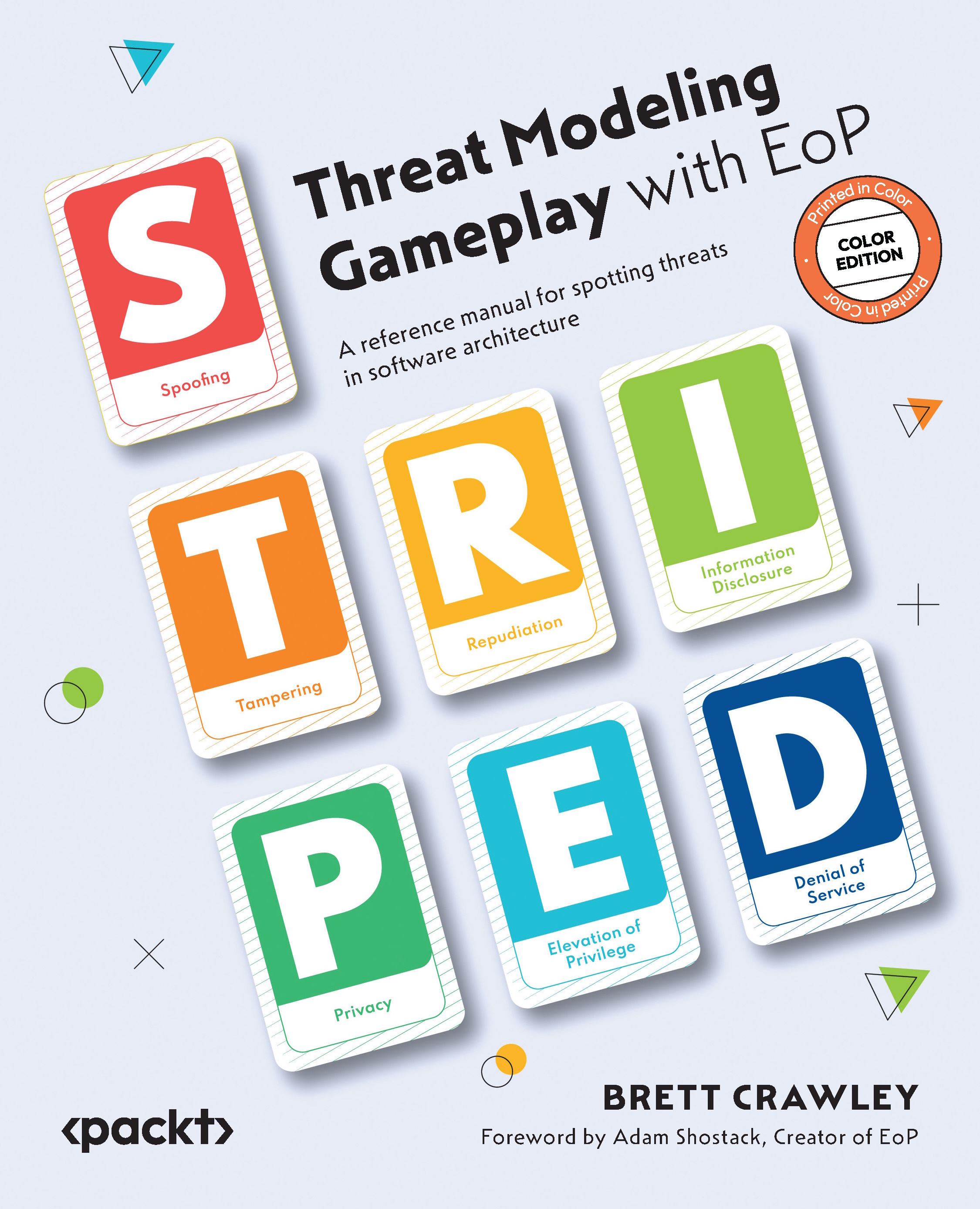
In the next chapter, we will cover the privacy extension that turns STRIDE into STRIPED and includes privacy threats...