Managing collaborative penetration testing using Faraday
One of the most difficult aspects of penetration testing is remembering to test all of the relevant parts of the network or system target, or trying to remember whether the target was actually tested after the testing has been completed. In some cases, a single client may have multiple penetration testers performing scanning activities from multiple locations, and management would like to have a single view. Faraday can provide this, assuming all of the penetration testers are able to ping each other on the same network or on the internet for external assessment.
Faraday is a multiuser penetration test Integrated Development Environment (IDE). It is designed for testers to distribute, index, and analyze all of the data that is generated during the process of a penetration test or technical security audit to provide different views, such as Management, Executive Summary, and Overall Issues lists.
This IDE platform was developed in Python by InfoByte, and version 3.14.3 is installed by default in the latest version of Kali Linux. You can navigate, from the menu, to Applications, click on 12-Reporting tools, and then click on Faraday start. It should open up a new screen for you to enter your password to perform service changes. You should now be presented with the following screen to set up a username and password for the Faraday web portal.
Once the username and password are both set, the application should open the web browser, pointing to http://localhost:5985/
You will now be able to create workspaces for each project. The next step is to make sure all the testers that are to utilize the Faraday client perform all the tasks by running faraday-client in the terminal; it should prompt you to enter the credentials for the application. Use the same credentials that you just created, and you should now be able to see the same screen as that displayed in Figure 1.47:
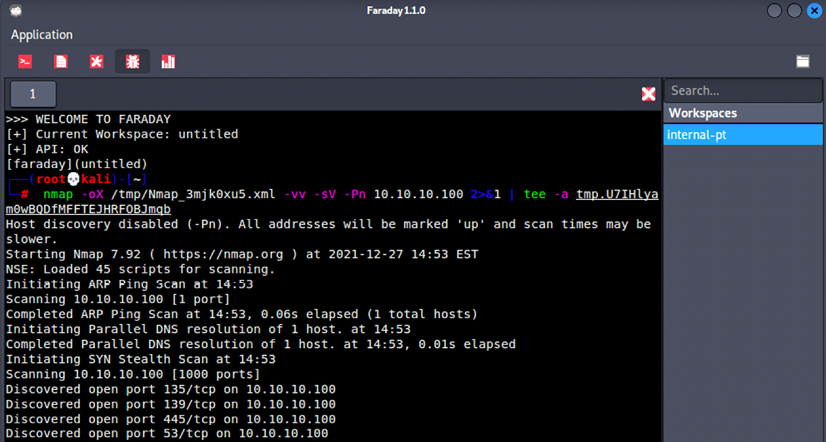
Figure 1.47: Running Nmap scan through the Faraday client
Following this screen, any scanning command-line activities that you or any other penetration testers in your team carry out can be visualized by clicking on the Faraday web application; this will display something similar to that shown in Figure 1.48:
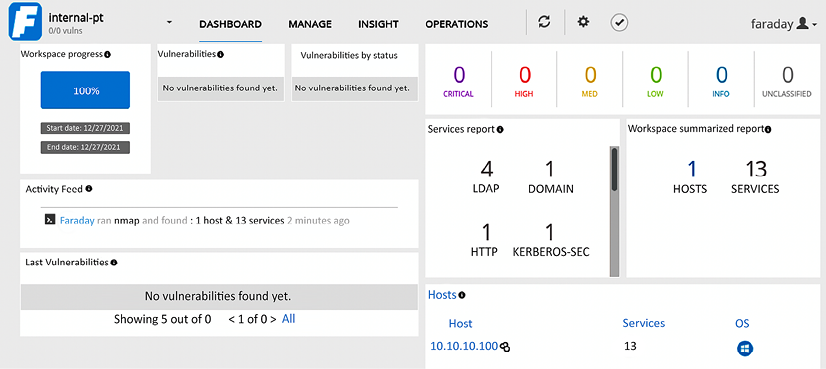
Figure 1.48: The real-time dashboard of Faraday
There is a limitation of the free version of Faraday 3.15.0, where real-time operations, insights, and data analysis cannot be utilized by testers to visualize the whole list of issues in a single place.

































































