As with the chain of custody/audit trail mentioned in the preceding section, the style of report writing will no doubt vary based on legislative demands, company or agency guidelines, and individual investigator style. Once again, it makes sense to have a good grounding in the basics of digital forensic report writing, so that you have a flexible skill set within which to work.
Reports may also differ significantly depending on who is going to end up reading them. If you are investigating a civil dispute, your final report will probably not be written in highly technical language and may just include an overview in layperson terms of the methodology used and what was uncovered. If you are going to be called into court as an expert witness however, then a higher level of technical detail and a more in-depth demonstration of your investigative processes will no doubt be needed.
Broadly speaking, most digital evidence reports should include the following:
- Name, job title, and company of the senior investigating officer.
- Name, job title, and company of the digital forensics examiner (if different from the preceding one).
- A brief description of the case, including the nature of the activities under investigation.
- Name of the person or persons whose devices or data are under investigation.
- Start and end date of the investigation.
- Methodology used throughout the investigation, including but not limited to how evidence was identified, collected, preserved, and analyzed. This may also include details of any tools and processes used, as well as a copy of the chain of custody.
- An overview of the results of the investigation in line with the original activities specified at the beginning of the report, as well as any other relevant information that was uncovered in the course of the investigation.
- Screenshots, printouts, or other evidential items that demonstrate the results of the case.
- An analysis of the results, including any conclusions regarding guilt or innocence of the accused party.
- Any appendices, glossaries, or other information that may prove useful to the reader of the report.
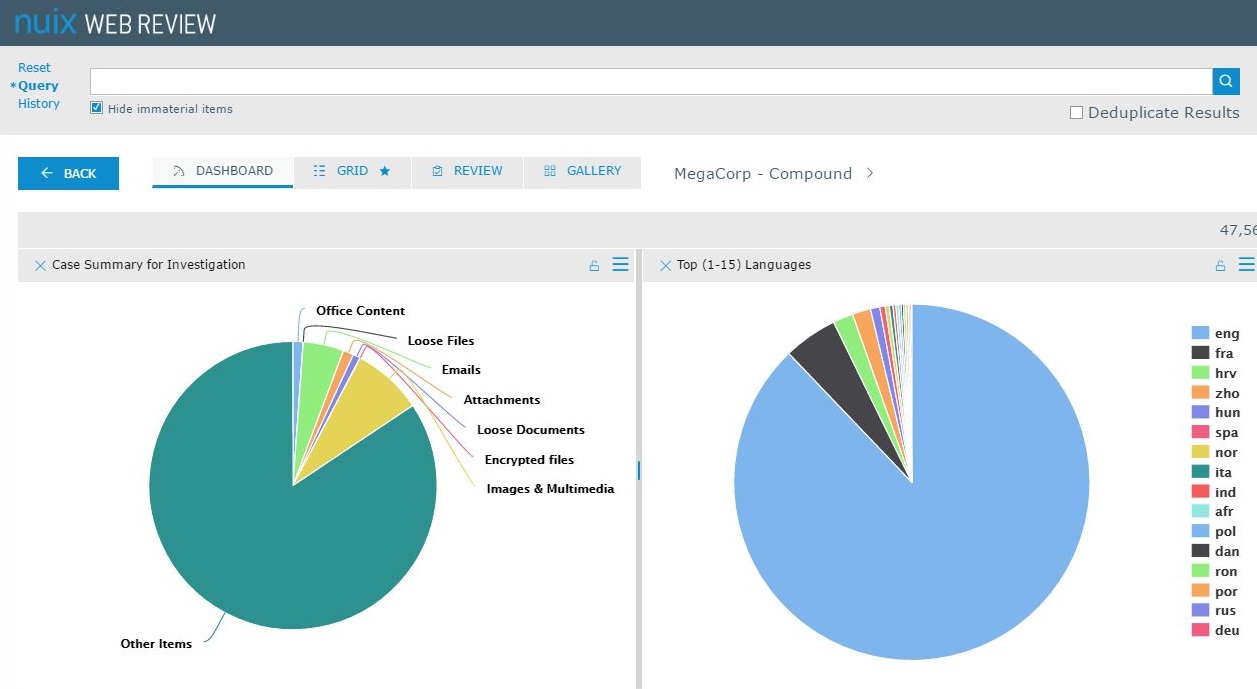
Many forensic tools will generate their own reports in either digital or printable formats, in a number of different styles such as PDFs, Excel documents, or Word files. Some software packages, such as Nuix's Investigator Suite, include add-ons like Web Review and Analytics, which allow for multiple users to view or work on the same case. This can be very useful during an investigation, as it allows an administrator or senior investigator to allocate certain roles within a case, but it can also come in handy when compiling reports. Some users can be given access only to the final report, which they can enter into and look at the results that have been found and compiled into user-friendly graphs; if they have the correct permissions, they can then also take a further look at the evidence from this. The following diagram shows the dashboard of the Nuix Web Review and Analytics interface, which allows users to view and manage evidence in a forensic investigation.