We'll take a look at how UDP works, what it is, and what's in the UDP header. The UDP protocol is a connectionless protocol and it's very lightweight—a very small header.
If you'd like to learn more about the UDP protocol, take a look at https://www.ietf.org/rfc/rfc768.txt:

This is the original specification. It's been updated since August 28, 1980, if you look through all of the RFCs, but the original specification is 768. If you'd like to learn about all the details of UDP, which are relatively short, you can do so through the file shown in the preceding screenshot.
Let's take a look at UDP in Wireshark:
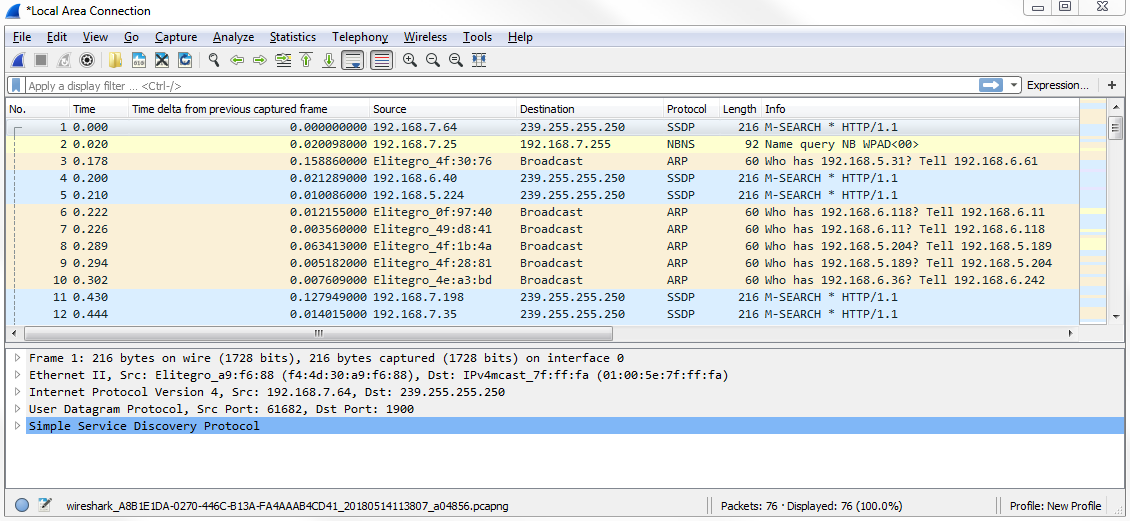
We have a capture of just a few seconds of data and a whole mixture of applications and protocols. What we can do is simply filter based on udp. If you press Enter, now it only shows UDP packets:

And you can see that...