Listing open ports on a remote host
This recipe describes the simplest way of using Nmap to determine the port states on a remote host, a process used to identify running services commonly referred as port scanning.
How to do it...
Open a terminal.
Type the following command:
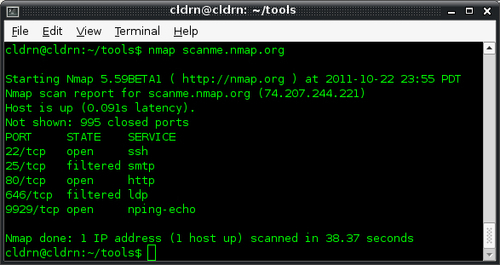
$ nmap scanme.nmap.org
The scan results should appear on the screen, showing the interesting ports and their states. The ports marked as open are of special interest as they represent services running on the target host.
How it works...
The following command checks the state of the most popular ports on the host scanme.nmap.org by launching a TCP port scan:
$ nmap scanme.nmap.org
The results contain host information such as the IPv4 address and PTR record, and port information such as a service name and port state.
There's more...
Even for this simplest port scan, Nmap does a lot of things in the background, and these can be configured as well.
Nmap begins by converting the hostname to an IPv4 address using DNS. If you wish to use a different DNS server, use --dns-servers <serv1[,serv2],...>, or use-n if you wish to skip this step, as follows:
$ nmap --dns-servers 8.8.8.8,8.8.4.4 scanme.nmap.org
Afterwards, it pings the target address to check if the host is alive. To skip this step use –PN as follows:
$ nmap -PN scanme.nmap.org
Nmap then converts the IPv4 address back to a hostname by using a reverse DNS call. Use -n to skip this step as follows:
$ nmap -n scanme.nmap.org
Finally, it launches a TCP port scan. To specify a different port range, use -p[1-65535], or -p- for all possible TCP ports, as shown in the following command:
$ nmap -p1-30 scanme.nmap.org
Privileged versus unprivileged
Running nmap <TARGET> as a privileged user launches the
SYN Stealth Scan. For unprivileged accounts that can't create raw packets, the
TCP Connect Scan is used.
The difference between these two is that a TCP Connect Scan uses the high-level system call connect to obtain information about the port state. This means that each TCP connection is fully completed and, therefore, is slower and more likely to be detected and recorded in system logs. SYN Stealth Scans use raw packets to send specially-crafted TCP packets that detect port states more reliably.
Port states
Nmap categorizes ports into the following states:
Note
The type of packets sent depends on the scanning technique(s) used.
Open: This indicates that an application is listening for connections on this port.
Closed: This indicates that the probes were received but there is no application listening on this port.
Filtered: This indicates that the probes were not received and the state could not be established. It also indicates that the probes are being dropped by some kind of filtering.
Unfiltered: This indicates that the probes were received but a state could not be established.
Open/Filtered: This indicates that the port was filtered or open but Nmap couldn't establish the state.
Closed/Filtered: This indicates that the port was filtered or closed but Nmap couldn't establish the state.
Port scanning techniques supported by Nmap
We showed the simplest way of performing a port scan, but Nmap has a vast number of advanced scanning techniques available. Use nmap -h or visit http://nmap.org/book/man-port-scanning-techniques.html to learn more about them.
See also
The Fingerprinting services of a remote host recipe
The Finding live hosts in your network recipe
The Scanning using specific port ranges recipe
The Scanning using a specified network interface recipe
The Manage different scanning profiles with Zenmap recipe
The Monitoring servers remotely with Nmap and Ndiff recipe
The Excluding hosts from your scans recipe in Chapter 2, Network Exploration
The Scanning IPv6 addresses recipe in Chapter 2, Network Exploration
The Fingerprinting the operative system of a host recipe in Chapter 3, Gathering Additional Host Information
The Discovering UDP services recipe in Chapter 3, Gathering Additional Host Information
The Listing protocols supported by a remote host recipe in Chapter 3, Gathering Additional Host Information
























































