Most web penetration testing happens in the client, that is, in the web browser; hence, we need to prepare our browser to make it a useful tool for our purposes. In this recipe, we will do that by adding several plugins to the Firefox browser installed in Kali Linux by default.
Configuring the web browser for penetration testing
How to do it...
Firefox is a very flexible browser that fits the purpose of web penetration testing very well; it also comes pre-installed in Kali Linux. Let's customize it a little bit to make it better using the following steps:
- Open Firefox and go to Add-ons in the menu:

- In the search box, type wappalyzer to look for the first plugin we will install:
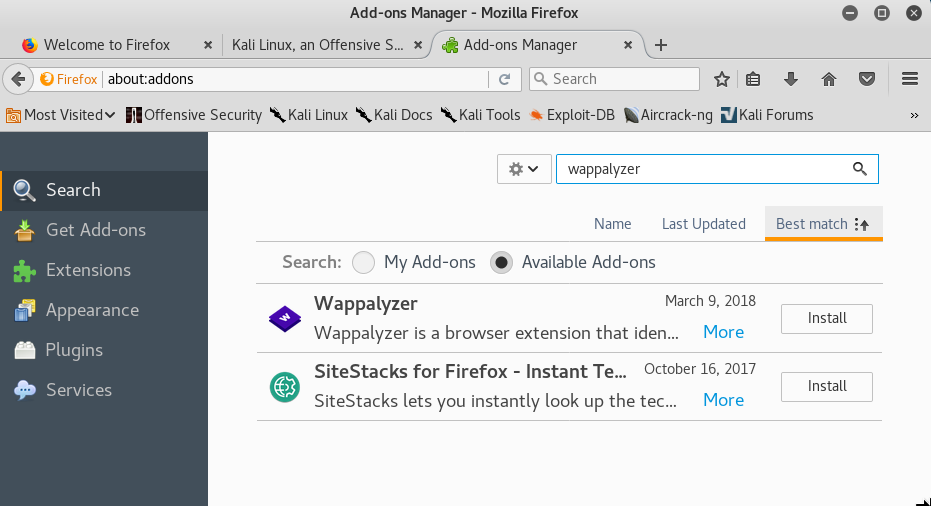
- Click Install in the Wappalyzer add-on to install it. You may also need to confirm the installation.
- Next, we search for FoxyProxy.
- Click on Install.
- Now search for and install Cookies Manager+.
- Search for and install HackBar.
- Search for and install HttpRequester.
- Search for and install RESTClient.
- Search for and install User-Agent Switcher.
- Search for and install Tampermonkey.
- Search for and install Tamper Data and Tamper Data Icon Redux.
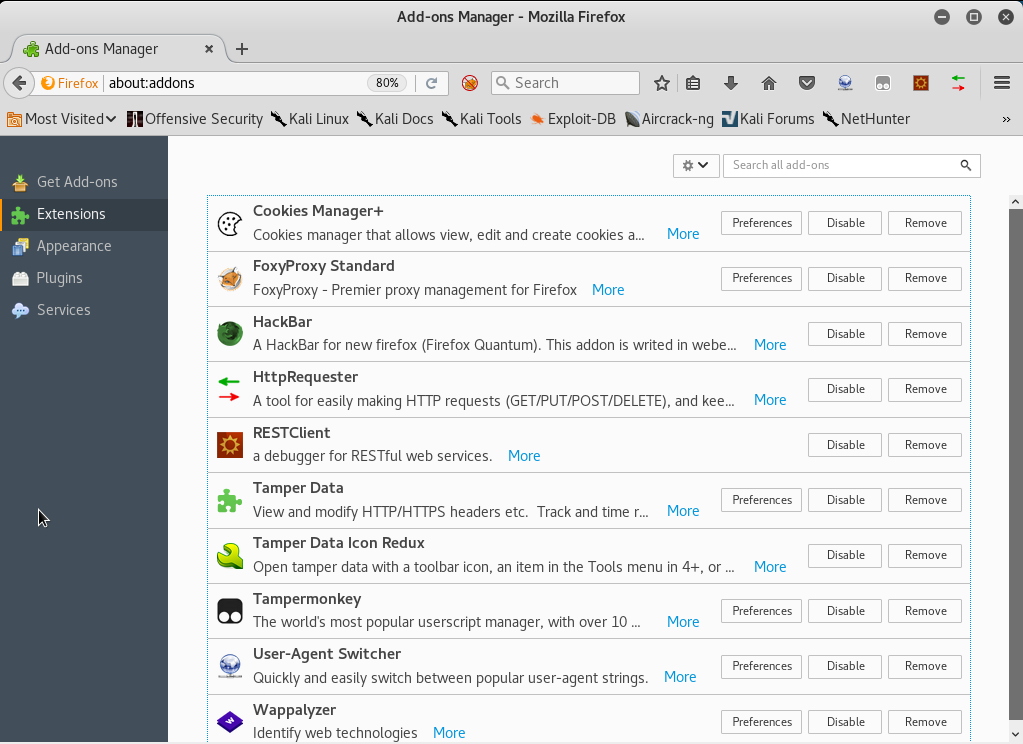
- The list of extensions installed should look like the following screenshot:
How it works...
So far, we've just installed some tools in our web browser, but what are these tools good for when it comes to penetration testing a web application? The add-ons installed are as follows:
- HackBar: A very simple add-on that helps us try different input values without having to change or rewrite the full URL. We will be using this a lot when doing manual checks for cross-site scripting and injections. It can be activated using the F9 key.
- Cookies Manager+: This add-on will allow us to view and sometimes modify the value of cookies the browser receives from the applications.
- User-Agent Switcher: This add-on allows us to modify the user-agent string (the browser identifier) that is sent in all requests to the server. Applications sometimes use this string to show or hide certain elements depending on the browser and operating system used.
- Tamper Data: This add-on has the ability to capture any request to the server just after it is sent by the browser, giving us the chance to modify the data after introducing it in the application's forms and before it reaches the server. Tamper Data Icon Redux only adds an icon.
- FoxyProxy Standard: A very useful extension that lets us change the browser's proxy settings in one click using user-provided presets.
- Wappalyzer: This is a utility to identify the platforms and developing tools used in websites. This is very useful for fingerprinting the web server and the software it uses.
- HttpRequester: With this tool, it is possible to craft HTTP requests, including get, post, and put methods, and to watch the raw response from the server.
- RESTClient: This is basically a request generator like HTTP requester, but focused on REST web services. It includes options to add headers, different authentication modes, and get, post, put, and delete methods.
- Tampermonkey: This is an extension that will allow us to install user scripts in the browser and make on-the-fly changes to web page content before or after they load. From a penetration testing point of view, this is useful to bypass client-side controls and other client code manipulations.
See also
Other add-ons that could prove useful for web application penetration testing are the following:
- XSS Me
- SQL Inject Me
- iMacros
- FirePHP