By definition, penetration testing is simulating external and internal attacks. The main goal of penetration testing is to enhance the security position of an organization.
Penetration testing overview
Penetration testing types
There are three categories of penetration testing:
- White box pentesting
- Black box pentesting
- Gray box pentesting
White box pentesting
During white box pentesting, or what's sometimes named complete-knowledge testing, the organization gives the pentesters all required information. This type of pentesting is used when the organization wants to perform a full audit of its security and maximize the testing time. It can be done at any point to check its security position. The information provided before performing the pentesting could be, and it is not limited to the following things:
- Network information: Network typology and diagrams, IP addresses, intrusion detection systems, firewalls, and access information
- Infrastructure: Both hardware and software information is made available to the pentesters
- Policies: This is really important because every pentester has to make sure that the pentesting methodology is aligned with the organization's policies
- Current security state including previous pentesting reports
Black box pentesting
In a black box pentesting session, the pentester simulates a real-world attack to gain access to a system or IT infrastructure. Thus, he opts for a pentesting approach with no information about the organization and no prior knowledge of the infrastructure. This type of pentesting is very effective because the pentester wears a black hat and uses a black hat hacker's techniques to bypass the organization's security guards. It is carried out from a black hat hacker's point of view. So, they use fingerprinting techniques to discover everything about the organization.
Gray box pentesting
Gray box pentesting involves simulating an attack by an insider. The pentester is given partial and limited information, like any normal user. This sort of testing lies between black box and white box pentesting.
The penetration testing teams
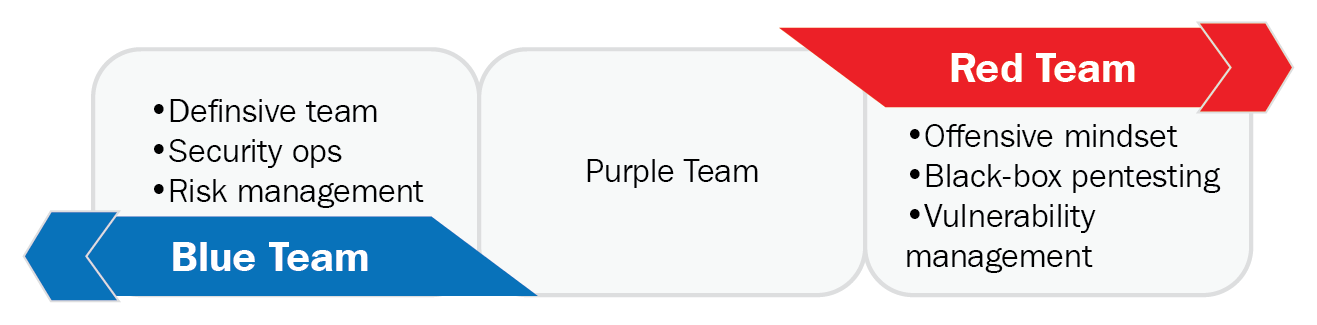
Red teaming and blue teaming are two concepts inspired by strategies used in the military.
Red teaming
The role of a red team is clear. They generally have a specific mission, which is testing the current state of physical and digital security of an organization. The members of a red team have an offensive mindset. They try to attack a specific area.
Blue teaming
Blue teams are the defensive layer. Their mission is to defend against the red team. In general, they are the internal security team.
Purple teaming
To ensure effective penetration testing, a new team is created named the purple team. This team has an effective approach to make the communication between red teams and blue teams clearer, as shown in the following figure: