Increasing the Windows attack surface
To further increase the availability of the attack surface on the Windows operating system, it is important to add vulnerable software and to enable or disable certain integrated components.
Getting ready
Prior to modifying the configurations in Windows to increase the attack surface, you will need to have the operating system installed on one of your virtual machines. If this has not been done already, please see the Installing Windows Server recipe in this chapter.
How to do it…
Enabling remote services, especially unpatched remote services, is usually an effective way to introduce some vulnerabilities into a system. First, you'll want to enable Simple Network Management Protocol (SNMP) on your Windows system. To do this, open the start menu in the bottom-left corner and then click on Control Panel. Double-click on the Add or Remove Programs icon and then click on the Add/Remove Windows Components link on the left-hand side of the screen to get the following screen:

From here, you will see a list of components that can be enabled or disabled on the operating system. Scroll down to Management and Monitoring Tools and double-click on it to open the options contained within, as shown in the following screenshot:

Once opened, ensure that both checkboxes for SNMP and WMI SNMP Provider are checked. This will allow remote SNMP queries to be performed on the system. After clicking on OK, the installation of these services will begin. The installation of these services will require the Windows XP image disc, which VMware likely removed after the virtual machine was imaged. If this is the case, you will receive a pop up requesting you to insert the disc as shown in the following screenshot:

To do this, access the virtual machine settings. Ensure that the virtual optical media drive is enabled, then browse to the ISO file in your host filesystem to add the disc:

Once the disc is detected, the installation of SNMP services will be completed automatically. The Windows Components Wizard should notify you when the installation is complete. In addition to adding services, you should also remove some default services included in the operating system. To do this, open Control Panel again and double-click on the Security Center icon. Scroll to the bottom of the page, and click on the link for Windows Firewall and ensure that this feature is turned off, as shown in the following screenshot:
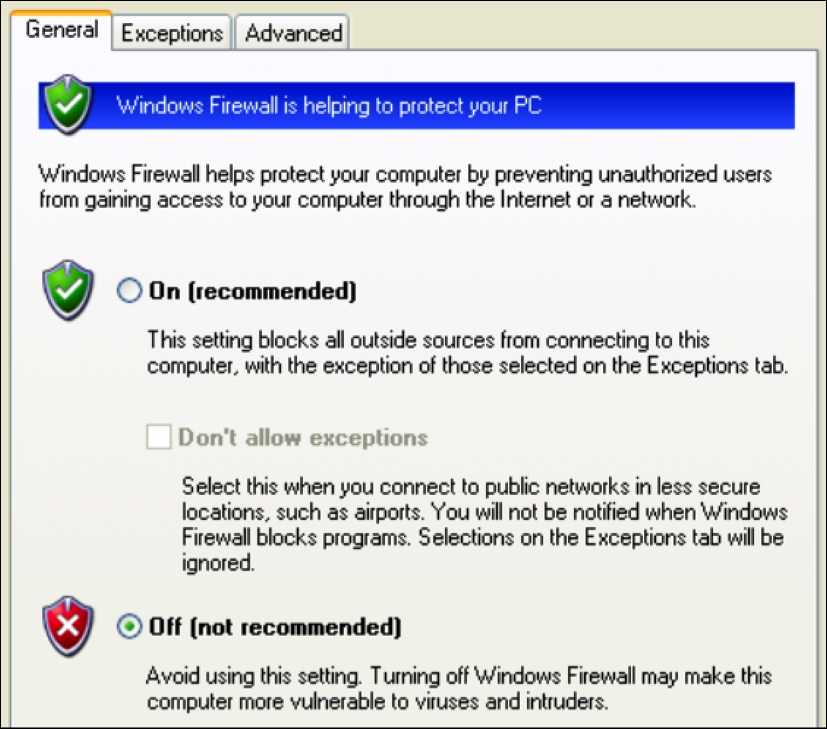
After you have turned off the Windows Firewall feature, click on OK to return to the previous menu. Scroll to the bottom once again, then click on the Automatic Updates link and ensure that it is also turned off.
How it works…
The enabling of functional services and disabling of security services on an operating system drastically increases the risk of compromise. By increasing the number of vulnerabilities present on the operating system, we also increase the number of opportunities available to learn attack patterns and exploitation. This particular recipe only addressed the manipulation of integrated components in Windows to increase the attack surface. However, it can also be useful to install various third-party software packages that have known vulnerabilities. Vulnerable software packages can be found at the following URLs:

































































