Conventions used
There are a number of text conventions used throughout this book.
Code in text: Indicates code words in text, database table names, folder names, filenames, file extensions, pathnames, CLI menu choices, commands, and user input. Here is an example: “When logged in to CPCM1, execute the command, set expert-password.”
A block of code or sequential uninterrupted commands is set as follows:
add host name host_test1 ip-address 10.0.0.111
add host name host_test2 ip-address 10.0.0.112
add host name host_test3 ip-address 10.0.0.113
When commands are shown in the context of a particular shell, are interactive, or are combined with step descriptions, they are shown like this:
# Step 1
show installer packages recommended
# Note the Display name of the package you are interested in.
# Step 2
show installer package
# [press spacebar and then press the Tab key]
# Note the Num(ber) corresponding to the Display name of the package from step 1.
Any command-line input or output is written as follows:
CPXXX> show date Date 02/02/2022 CPXXX > show time Time 18:19:17 $ cd css
Bold indicates a new term, an important word, or words that you see onscreen. For instance, words in menus or dialog boxes appear in bold. Here is an example: “Once the Plugins Admin window is opened, scroll down until you see Compare and check the checkbox.”
Italics indicates either internal or external references, such as “In Chapter 7, SmartConsole – Familiarization and Navigation, we saw how to do that using the management CLI.” It is also used to denote a specific keypress, such as “press Enter.”
Additionally, italics are used to indicate an emphasis on specifics, such as in the following sentence: “Even though the domain objects are defined, created, and modified in SmartConsole, we must use associated CLI tools on the gateways where the policies containing these objects are installed, and not on the management server.”
[#], [A], and [a] indicate the numerical or letter-based points of interest in figures (screenshots), typically referencing screenshots following the text, unless explicitly noted otherwise, as follows:
“To illustrate how to create additional server objects (also referred to as a Check Point Host object), let’s click on the New icon [1] in the Actions menu of the GATEWAYS & SERVERS view, click More [2], and then click Check Point Host… [3]:”
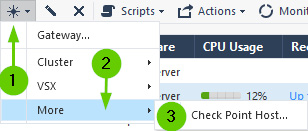
Sample image showing [] instances
Keywords are used whenever a new important term is used in the context of the chapter or a section, such as: “Access roles are the ultimate tool for the implementation of the zero-trust concept in your environment.”
Tips or Important Notes
Appear like this.