Decrypting wireless network traffic
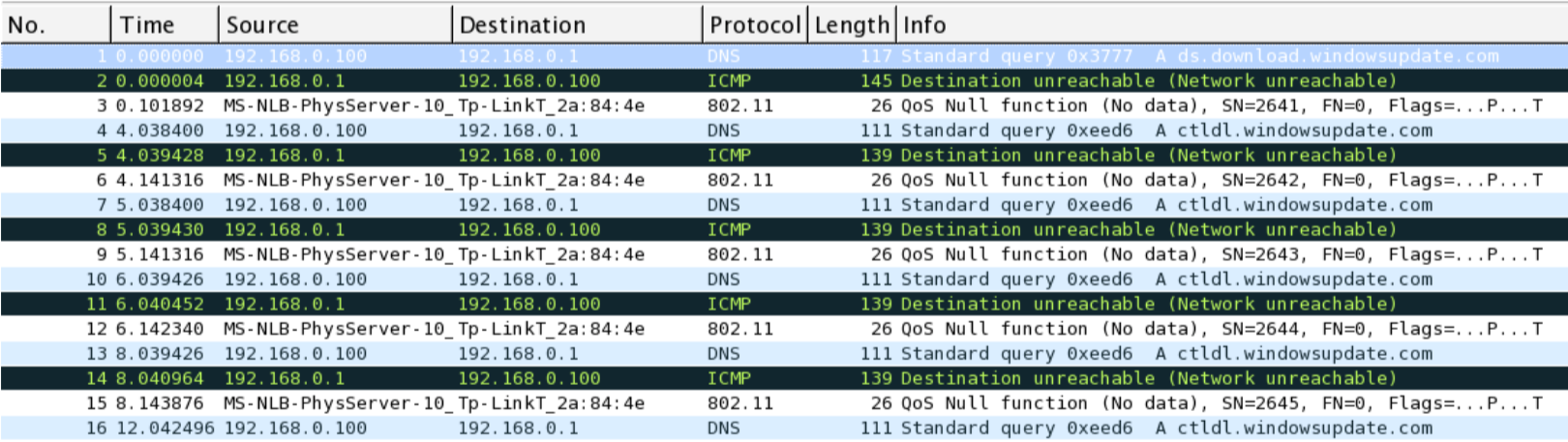
Wireshark also facilitates decryption of wireless traffic through embedding a pre-shared key under the 802.11 protocol section. The following screenshot depicts normal wireless traffic being sniffed from a nearby access point:
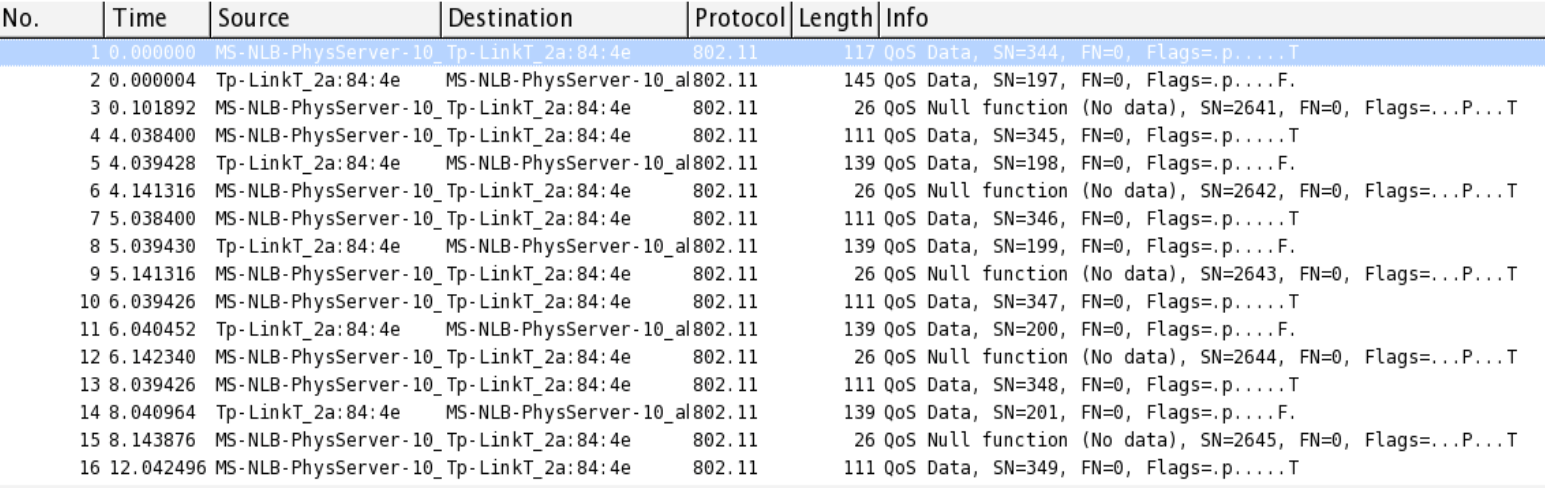
WLAN traffic before decryption
In order to decrypt the preceding listed packets, we need to configure the IEEE 802.11 section as follows:
- Go to
Edit|Preferences, expand theProtocolsection, selectIEEE 802.11and configure it as follows:

- Click on the
Editbutton next toDecryption Keys. - Click on
Newand add theWEP/WPAkey to enable decryption. After all the changes have been made, click onOK:

Now you will be shown the decrypted traffic as follows:
WLAN traffic after decryption