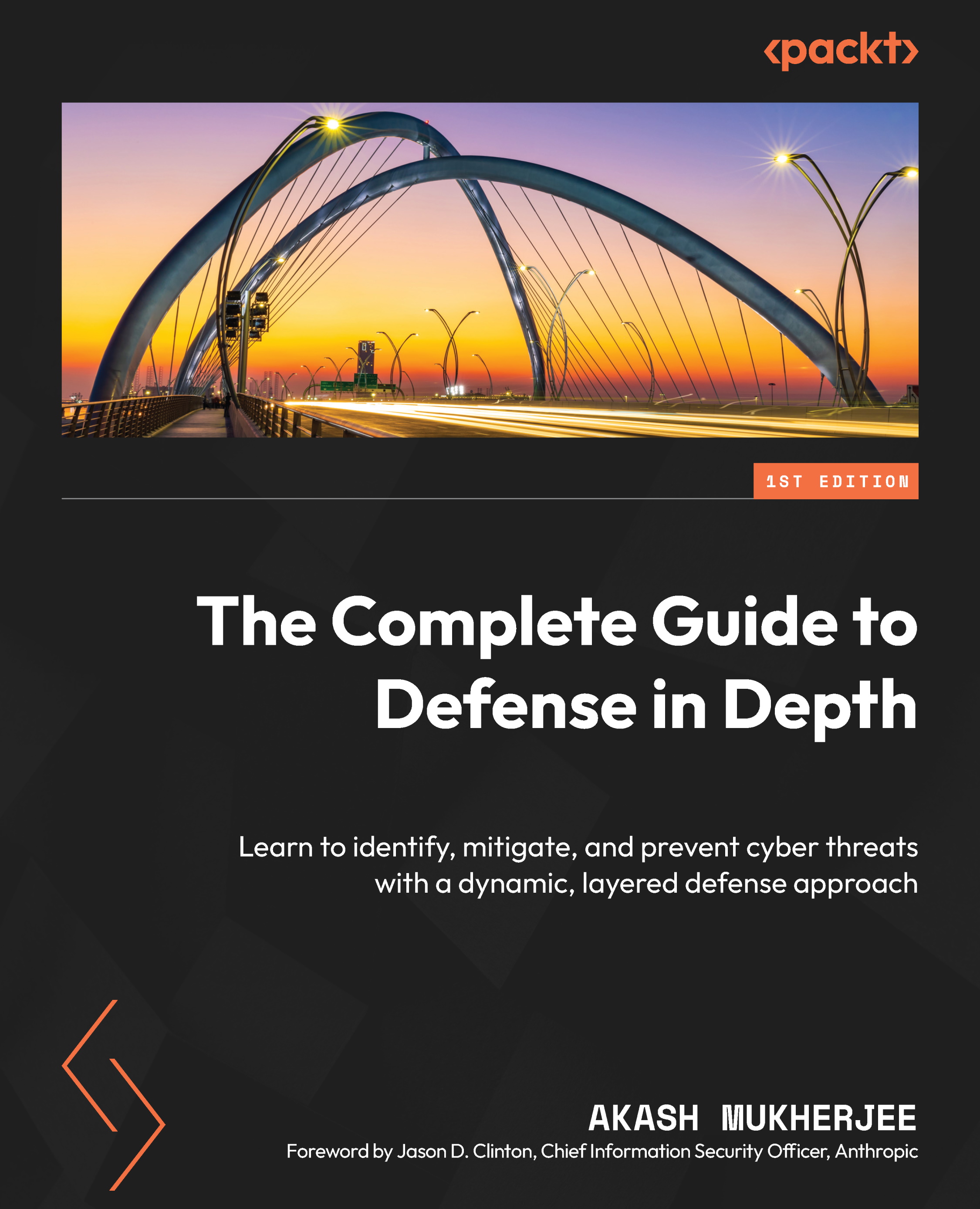
Akash Mukherjee is a security enthusiast and a leader with experience setting up and executing security strategies at large tech companies. He is currently a security leader at Apple AIML. He was previously a security lead at Google, leading the insider risk program and supply chain security efforts at Google Chrome. During his time at Google, Akash was also a course lead and subject matter expert for the Google Cybersecurity Certificate course. He has been at the forefront of the emerging threat landscape and has led the development of novel security strategies and frameworks. Akash was one of the co-developers of the open-source Supply-chain Levels for Soft ware Artifacts (SLSA) framework.
He is based in the Silicon Valley area in the US, and he holds a bachelor of technology degree from the Indian Institute of Technology, B.H.U., India, and a master's degree in cyber security from the University of Southern California, USA.
Read more
 United States
United States
 Great Britain
Great Britain
 India
India
 Germany
Germany
 France
France
 Canada
Canada
 Russia
Russia
 Spain
Spain
 Brazil
Brazil
 Australia
Australia
 Singapore
Singapore
 Hungary
Hungary
 Ukraine
Ukraine
 Luxembourg
Luxembourg
 Estonia
Estonia
 Lithuania
Lithuania
 South Korea
South Korea
 Turkey
Turkey
 Switzerland
Switzerland
 Colombia
Colombia
 Taiwan
Taiwan
 Chile
Chile
 Norway
Norway
 Ecuador
Ecuador
 Indonesia
Indonesia
 New Zealand
New Zealand
 Cyprus
Cyprus
 Denmark
Denmark
 Finland
Finland
 Poland
Poland
 Malta
Malta
 Czechia
Czechia
 Austria
Austria
 Sweden
Sweden
 Italy
Italy
 Egypt
Egypt
 Belgium
Belgium
 Portugal
Portugal
 Slovenia
Slovenia
 Ireland
Ireland
 Romania
Romania
 Greece
Greece
 Argentina
Argentina
 Netherlands
Netherlands
 Bulgaria
Bulgaria
 Latvia
Latvia
 South Africa
South Africa
 Malaysia
Malaysia
 Japan
Japan
 Slovakia
Slovakia
 Philippines
Philippines
 Mexico
Mexico
 Thailand
Thailand