We will use the official Kali Linux official ISO provided by Offensive Security to install and configure different desktop environments.
Configuring Kali Linux
Getting ready
To start with this recipe, we will use the 64-bit Kali Linux ISO listed on the Offensive Security website: https://www.kali.org/downloads/.
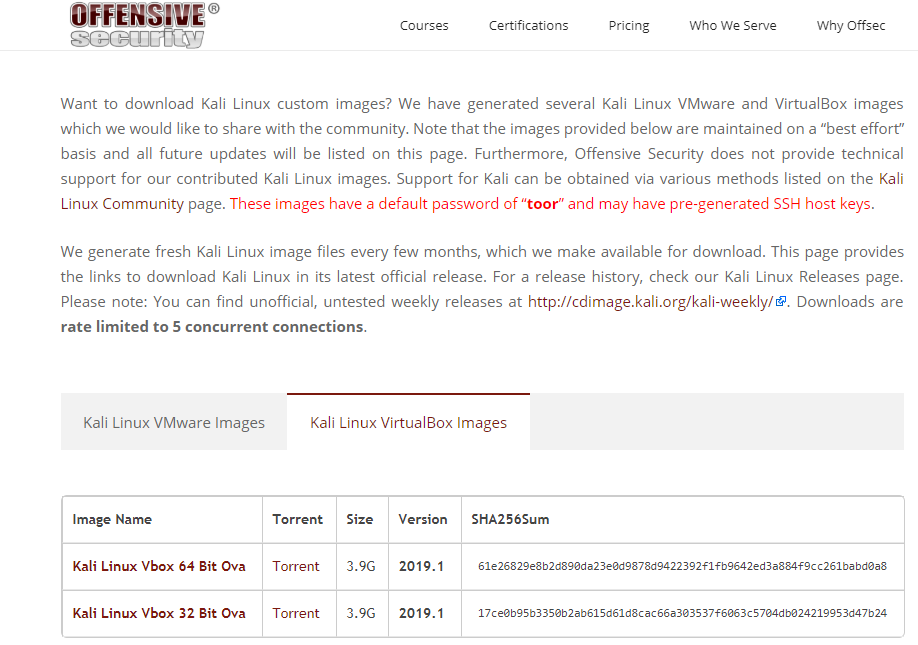
For users looking to configure Kali for a virtual machine such as VMware and VirtualBox, a prebuilt image of the Linux can be downloaded from the following URL: https://www.offensive-security.com/kali-linux-vmware-virtualbox-image-download/.
We will use the virtual image in this chapter and customize it with some additional tools. We can download it from the website, as shown in the following screenshot:
How to do it...
- Double-click the VirtualBox image; it should open with VirtualBox.
- Click Import.
- Start the machine and enter the password toor.
- Now, Kali is by default configured with Gnome Desktop Environment.
How it works...
With the prebuilt image, you don't need to worry about the installation process. You can consider it as a ready-to-go solution. Simply click on Run and the virtual machine will boot up the Linux just like a normal machine.