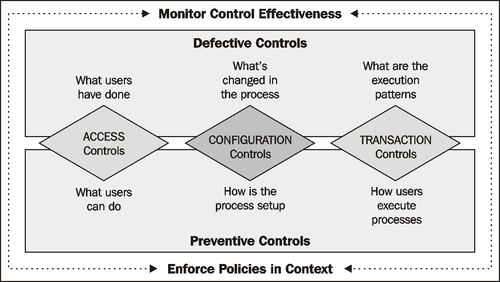
Automated application controls using Oracle GRC Controls Suite
Oracle GRC Controls Suite consists of the following four modules:
Application Access Controls Governor (AACG)
Transaction Controls Governor (TCG)
Configuration Controls Governor (CCG)
Preventive Controls Governor (PCG)
The following figure provides a view of the GRC Controls Suite:
Oracle Application Access Controls Governor
Oracle Application Access Controls Governor (AACG) is a segregation of duties, control authoring, and handling solution that works within and across ERP systems, such as Oracle E-Business Suite and PeopleSoft—to detect and prevent incidents of user access control violations. It can also be extended to monitor user access incidents in other off-the-shelf, custom and legacy applications including J D Edwards, SAP, and Salesforce. Each AACG control specifies "entitlements" to a company's business-management applications that should not be assigned simultaneously to individual users. AACG then finds users whose access...