Footer
In this recipe, we are going to go over the ZAP Proxy footer section and what each section does.
Getting ready
For you to be able to go over this recipe, you will need to have ZAP installed on your computer and you also need to have it started and running.
How to do it…
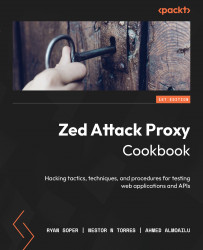
In the footer of ZAP proxy, you have three sections: Alerts, proxy status, and scan status. The Alerts section, as seen in Figure 2.25, gives you a quick view of any findings ZAP might have located on the application being tested.
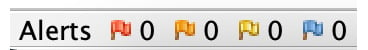
Figure 2.25 – Alerts
Then, we have proxy status, which shows what IP address and port the ZAP proxy is running on:
Figure 2.26 – The Proxy information
Lastly, we have a current scan status section, which shows what scan is currently running and what ZAP proxy is doing at any point of the scan process.

Figure 2.27 – The Current Scan Activity count
How it works…
The footer helps to track quick metrics on scanning and alerting data and is a quick way to ensure your established connection hasn’t changed. Consider highlighting this data when building executive reports, if some statistics are needed for a monthly key performance indicator (KPI) report, or even to help track data for vulnerability management.
In the next couple of recipes, we’ll discuss the Encode/Decode/Hash dialog and Fuzzer. We decided to go over these as many users of another prominent proxying tool are used to using these tabs, which are contained in ZAP in a different way. In order for you to carry out the attacks, we will discuss these in depth next.