Having a Windows operating system in your testing lab is critical to learning security skills as it is the most prominent operating system environment used in production systems. In the scenarios provided, an installation of Windows XP Service Pack 2 (SP2) is used. Since Windows XP is an older operating system, there are many flaws and vulnerabilities that can be exploited in a test environment.
Installing Windows Server
Getting ready
To complete the tasks discussed in this recipe and some of the exercises later in this book, you will need to acquire a copy of a Windows operating system. If possible, Windows XP SP2 should be used because it was the operating system used while writing this book. One of the reasons this operating system was selected is because it is no longer supported by Microsoft and can be acquired with relative ease and at little to no cost. However, because it is no longer supported, you will need to purchase it from a third-party vendor or acquire it by other means. I'll leave the acquisition of this product up to you.
How to do it...
Let's install Windows XP on the VM:
-
After booting from the Windows XP image file, a blue menu screen will load, which will ask you a series of questions to guide you through the installation process. Initially, you will be asked to define the partition that the operating system will be installed to. Unless you have made custom changes to your virtual machine, you should only see a single option here. You can then select either a quick or full-disk format. Either option should be sufficient for the virtual machine.
- Once you have answered these preliminary questions, you will be provided with a series of questions regarding operating system configurations. Then, you will be directed to the following screen:
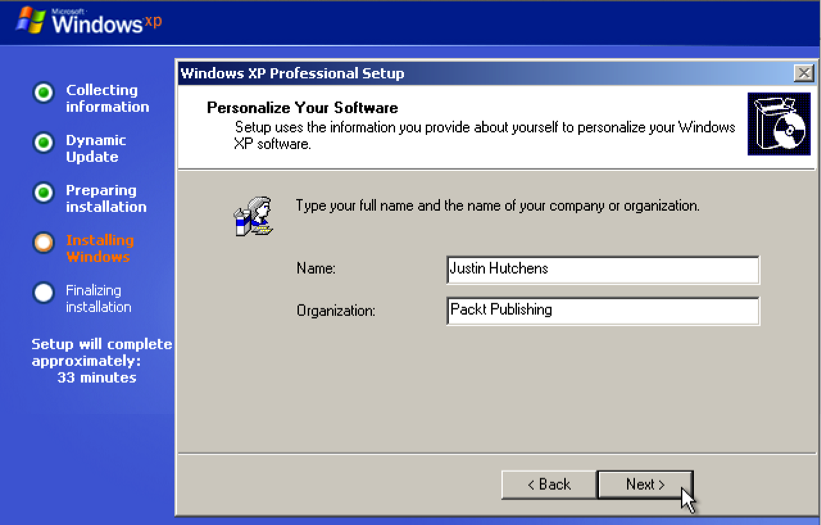
- First, you will be asked to provide a Name and Organization. The name is assigned to the initial account that was created, but the organization name is merely included for metadata purposes and has no effect on the performance of the operating system.
- Next, you will be requested to provide the Computer name and Administrator password, as shown in the following screenshot:
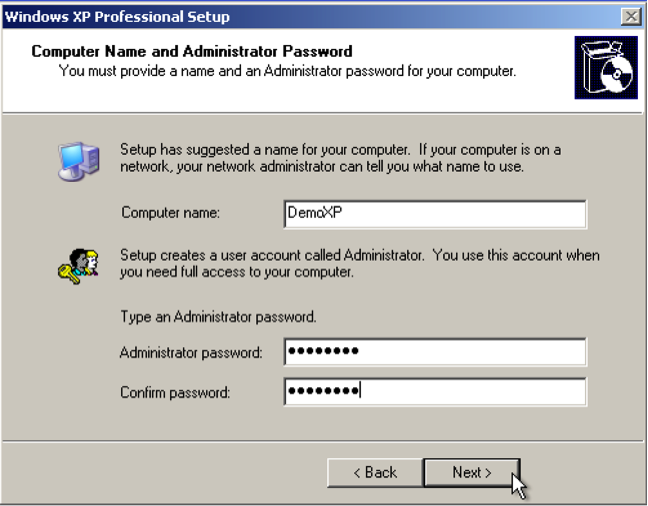
- If you will be adding the system to a domain, it is recommended you use a unique computer name. The admin password should be one that you will remember as you will need to log in to this system to test or configure changes. You will then be asked to set the date, time, and time zone. These will likely be automatically populated, but ensure that they are correct as misconfiguring the date and time can affect system performance. Have a look at the following screenshot:
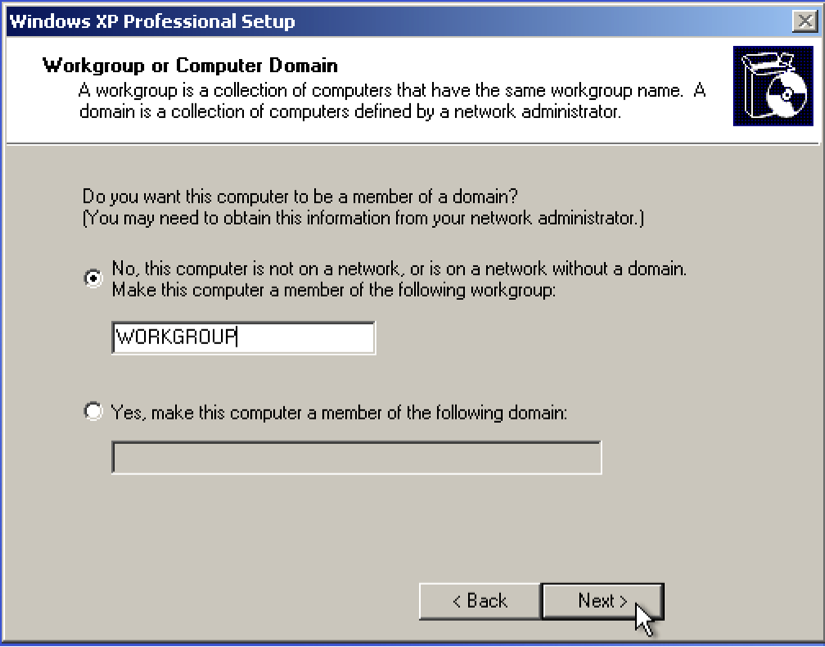
- After configuring the time and date, you will be asked to assign the system to either a workgroup or domain. Most of the exercises discussed within this book can be performed with either configuration. However, there are a few remote SMB auditing tasks, which will be discussed, that require that the system be domain joined. The following screenshot shows the Help protect your PC window:
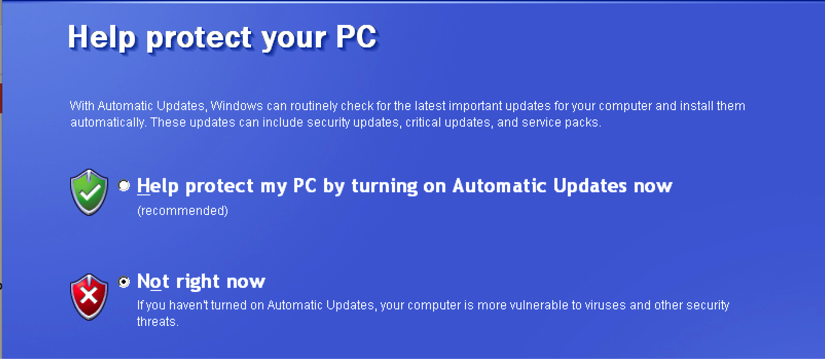
- After the installation process has been completed, you will be prompted to help protect your PC with automatic updates. The default selection for this is to enable automatic updates. However, because we want to increase the number of testing opportunities available to us, we will select the Not right now option.
How it works...
Windows XP SP2 is an excellent addition to any beginner's security lab. Since it is an older operating system, it offers a large number of vulnerabilities that can be tested and exploited. However, as one becomes more skilled in the art of penetration testing, it is important to begin to further polish your skills by introducing newer and more secure operating systems such as Windows 7.