To get started, we will have to actually create a policy. The process of assigning a policy is quite simple and can be covered by the following steps:
- Search for the Subscriptions blade—the easiest way to do so is to use the search field at the top of the Azure portal, as shown in the following screenshot:
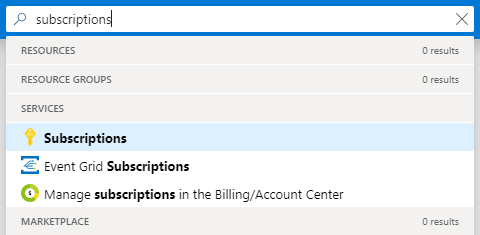
Figure 1.7 - Searching for the Subscriptions blade
- Select the subscription you are interested in. The last thing you need to do is to click on the Policies blade:
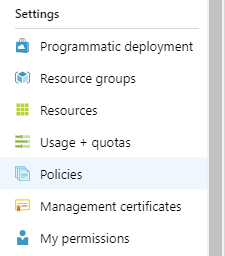
FIgure 1.8 - The Policies blade
- Click on the Assign policy button, which will display a form where you can define how the policy should work:

Figure 1.9 - The Assign policy button
- Assign a policy and configure the appropriate fields as follow: set the Scope of your subscription (in my case, it is Pay-As-You-Go) and leave the exclusions empty and the policy definition as Not allowed resource types. Remember that you can select either a built-in or a custom policy (if you have one).
- Initially, the compliance state may be displayed as Not registered as in the following screenshot. Wait a few minutes before proceeding:

Figure 1.10 - Created policies view
- If this status is diplayed longer than a few minutes, make sure a proper resource provider for the policies is registered. To do so, go to the Resource providers blade and check the status of the provider:

Figure 1.11 - Subscription resource providers
- Once the status is displayed as Registered, you can test the results. Try to perform a forbidden action (such as creating a forbidden resource type). If you do so, you will see a result similar to the following:

Figure 1.12 - Validation error
When a policy is enabled and working, it constantly monitors your resources against configured parameters. Depending on its configuration, it may either block deploying particular services or enforce a specific naming convention. An audit policy can report on non-compliant resources and, with enforcement mode enabled, can deny the creation of resources that don't comply with the policy.
Let's now check what a policy validation result may look like.