CloudGoat
CloudGoat is an AWS deployment tool that is designed by Rhino Security Labs. This tool is written in Python, which deploys a purposefully vulnerable AWS resource in the account. We will set up the CloudGoat Docker image within Kali Linux and explore the different vulnerabilities that attackers can take advantage of in a misconfigured cloud environment.
To make sure that CloudGoat can deploy the AWS resources, the first step is to possess a valid AWS account. Assuming that we have one from the Kali on AWS Cloud section, we will perform the following steps:
- Access https://console.aws.amazon.com/iam/home?region=us-east-2#/home.
- Click on the users, then on Add user; enter
cloudgoatand select Programmatic access; click Next, which should bring us to the screen shown in Figure 1.42:
Figure 1.42: Creating an IAM user account in the AWS console
- Select Attach existing policies directly and check AdministratorAccess, as shown in Figure 1.43; click on Next:

Figure 1.43: Adding the IAM user to the AdministratorAccess group
- Click on Next until you reach the final stage. If no error is displayed, then you should see the following screen with the Success message, where you can download the user Access key ID and Secret access key:

Figure 1.44: Creation of an Access key ID for the IAM user
Now that we have created the IAM user with administrative privileges within the AWS account, let us go ahead and install CloudGoat on the Docker image within Kali Linux by running the following commands in the terminal:
sudo apt install docker.io
sudo docker pull rhinosecuritylabs/cloudgoat
sudo docker run -it rhinosecuritylabs/cloudgoat:latest
Finally, configure the AWS client to connect to our AWS infrastructure using aws configure --profile masteringkali with the latest access key and secret that we downloaded from AWS, as shown in Figure 1.45. We will be exploring this tool in more detail in Chapter 8, Cloud Security Exploitation:
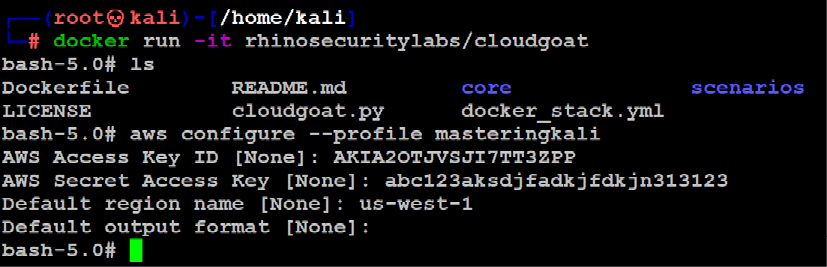
Figure 1.45: Configuration of AWS client for our newly created access key
Figure 1.46 depicts the LAB architecture of our setup for practicing penetration testing on our defined targets:

Figure 1.46: Our Mastering Kali Linux practice lab architecture
We have successfully built our own virtualized internal lab, and this should provide us with a wide range of exposure to identify and exploit multiple vulnerabilities within the infrastructure, application, and cloud. We should have the following set up:
- A Domain Controller running on Windows Server 2016 running Mutillidae through XAMPP
- A vulnerable on-premises Microsoft Exchange server running on Windows Server 2016 with missing patches.
- An obsolete Microsoft Windows 2008 R2 (Metasploitable3 server) running multiple vulnerable services.
- One domain administrator, one exchange administrator, and a normal domain user – which we will utilize in the latter part of this book to perform privilege escalation based on the roles.
- The AWS cloud deployment tool on a Docker image to set up vulnerable AWS infrastructure resources.
Testers have to ensure that all the VMs that are created as part of this lab network should always have the settings of the network set to NAT network and the network name as InsideNetwork, so that the VMs can communicate with each other.
































































