Metasploitable2 is an intentionally vulnerable Linux distribution and is also a highly effective security training tool. It comes fully loaded with a large number of vulnerable network services and also includes several vulnerable web applications.
Installing Metasploitable2
Getting ready
Prior to installing Metasploitable2 in your virtual security lab, you will need to download it from the Web. There are many mirrors and torrents available for this. One relatively easy method to acquire Metasploitable2 is to download it from SourceForge from this URL: http://sourceforge.net/projects/metasploitable/files/Metasploitable2/.
How to do it...
Installing Metasploitable2 is likely to be one of the easiest installations that you will perform in your security lab. This is because it is already prepared as a VMware virtual machine when it is downloaded from SourceForge.
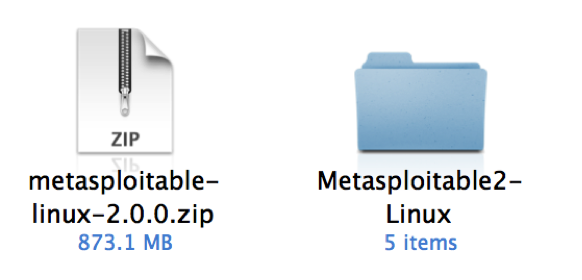
- Once the ZIP file has been downloaded, you can easily extract its contents on Windows or macOS by double-clicking on it in Explorer or Finder, respectively. Have a look at the following screenshot:
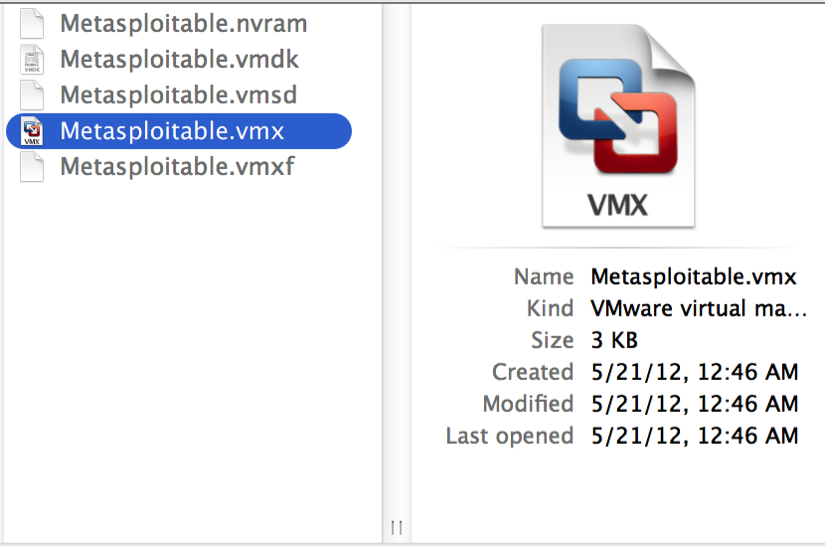
- Once extracted, the ZIP file will return a directory with five additional files inside. Included among these files is the VMware VMX file. To use Metasploitable2 in VMware, just click on the File drop-down menu and click on Open. Then, browse to the directory created from the ZIP extraction process, and open Metasploitable.vmx, as shown in the following screenshot:
- Once the VMX file has been opened, it should be included in your virtual machine library. Select it from the library and click on Run to start the VM and get the following screen:

- After the VM loads, the splash screen will appear and request login credentials. The default credentials are msfadmin for both the username and password. This machine can also be accessed via SSH, as addressed in the Configuring and using SSH recipe later in this recipe.
How it works...
Metasploitable was built with the idea of security testing education in mind. This is a highly effective tool, but it must be handled with care. The Metasploitable system should never be exposed to any untrusted networks. It should never be assigned a publicly routable IP address, and port forwarding should not be used to make services accessible over the Network Address Translation (NAT) interface.