Say no to SQL – owning MongoDBs
MongoDB is a free open source cross-platform database program. It uses JSON-like documents with schemas. The default security configuration of MongoDB allows anyone to access data unauthenticated. In this recipe, we will see how to exploit this vulnerability.
Getting ready
MongoDB runs on port 27017 by default. To access MongoDB, we need to download and install the MongoDB client. There are multiple clients available; we will use Studio-3T, which can be downloaded from https://studio3t.com/.
How to do it...
Follow the steps to learn about it:
- Once installed, we open the app and choose
Connect. - In the window that opens up, we click on a new connection:
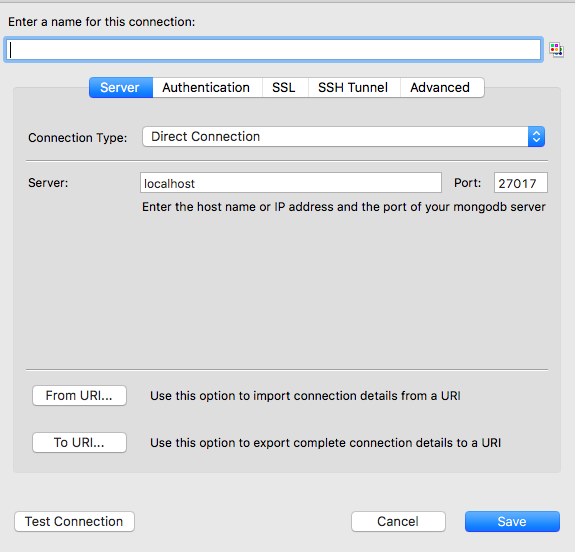
- Then, we choose a name, enter the IP address in the
Serverfield, and click onSave:
- Next, we simply select the database we just added from the list and click on
Connect. On successful connection, the database names will be displayed on the left-hand side and data will be displayed on the right-hand side.

























































