Crawling with the Spider
Spidering builds upon the Setting project options section, and we’ll use this to crawl the OWASP Juice Shop proxy. Crawling with the Spider allows us to identify directories on in-scope applications. This is useful to identify what is readily available and is visible to the user from the public-facing internet. ZAP will be able to provide better results to a user, allowing you to have a better understanding of a web application to perform a more complete, passive, and active scan.
Getting ready
To start, ensure that ZAP is started and OWASP Juice Shop is running.
How to do it…
After you’ve added which application to add to your scope, we need to select the URL. Right-click and select Spider. As shown in the screenshot of Figure 3.4, several options are shown by right-clicking on the URL in the Sites or Contexts sections.
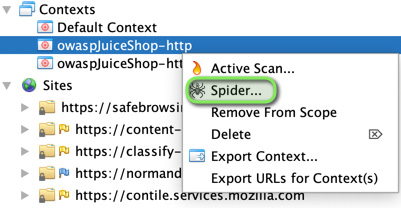
Figure 3.4 – Spidering from scope
Once you’ve selected your scope...