AI-assisted decision-making in pentesting
This section will tie together everything you’ve learned so far about ML and AI. We’ll be creating a customized AI agent that can make intelligent decisions, including which Metasploit modules and exploits may be applicable:
- In the RAGFlow web interface, create a new chat assistant. Name it
Pentest Hero, and use the settings found in the following figure for Assistant Setting.
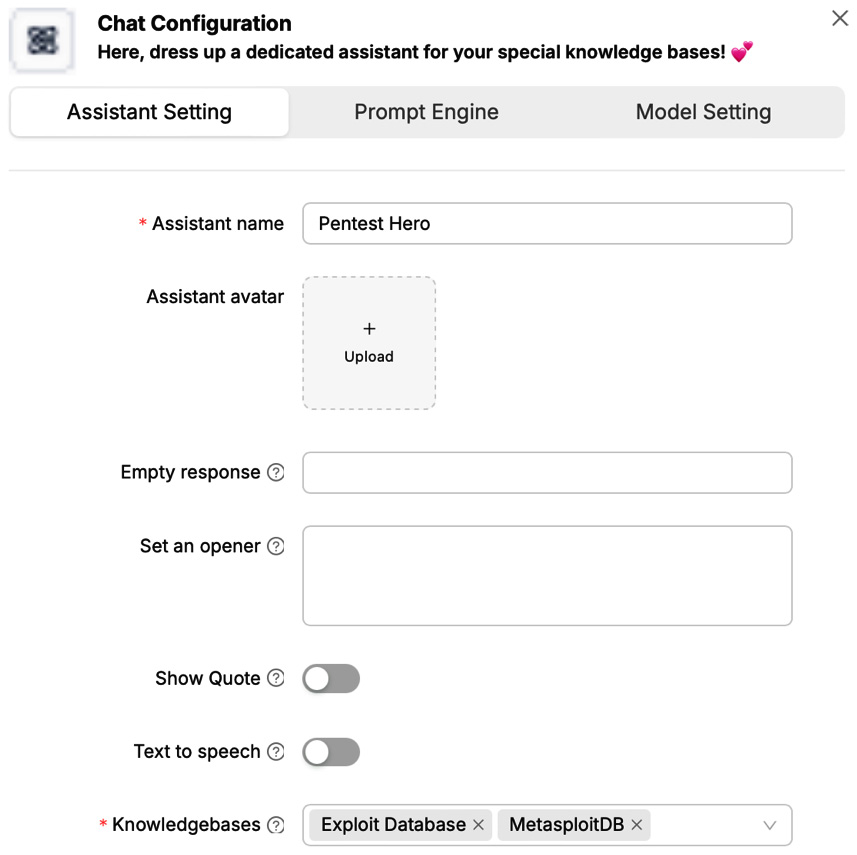
Figure 15.10 – Pentest Hero assistant settings are shown
- In the Prompt Engine tab, enter the following text in System prompt. This text can also be found in this chapter’s GitHub repository as
ch15_pentest_hero_prompt.txt:Your job is to take the data submitted to you in chat and compare each Nmap open port and service to your knowledge bases. One knowledge base contains Metasploit modules. The other knowledge base contains The Exploit Database exploits. Review these knowledge bases then compare...
































































