Segregation exercise
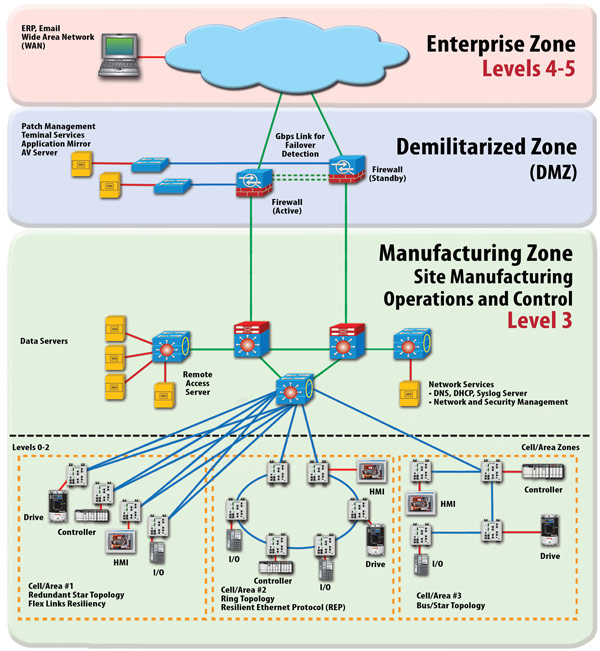
Absolute adherence to the bubble model will theoretically guarantee the integrity and security of any system in the secured area. In practice though, this can become a daunting task, especially as the size of the secured area increases. To make the task at hand more manageable, one must carefully determine what systems should go into the secured area (the CPwE-defined manufacturing zone) and which should stay out (placed in the enterprise zone).
As a rule of thumb, systems that cannot be secured by conventional strategies, such as patching and Antivirus deployment, should be placed in the manufacturing zone. For the remaining systems, it should be determined whether placing them in the enterprise zone versus the manufacturing zone has an adverse effect on the operability of the ICS or the amount of traffic to flow through the conduit (IDMZ), which dictates whether that system is to be placed in the manufacturing zone or the enterprise zone:
As an example, consider an ICS...


























































