Authentication NTLM versus Kerberos
NT LAN Manager (NTLM) and Kerberos are both authentication protocols that do not play any role in terms of authorization. NTLM is a proprietary authentication protocol developed by Microsoft, whereas Kerberos is a standard protocol. Starting with Win2K, Microsoft implements Kerberos as the default authentication protocol for the Windows OS. However, if the Kerberos protocol is not negotiated for some reason, then Active Directory (AD) will use LM, NTLM, orNTLM version 2(NTLMv2).
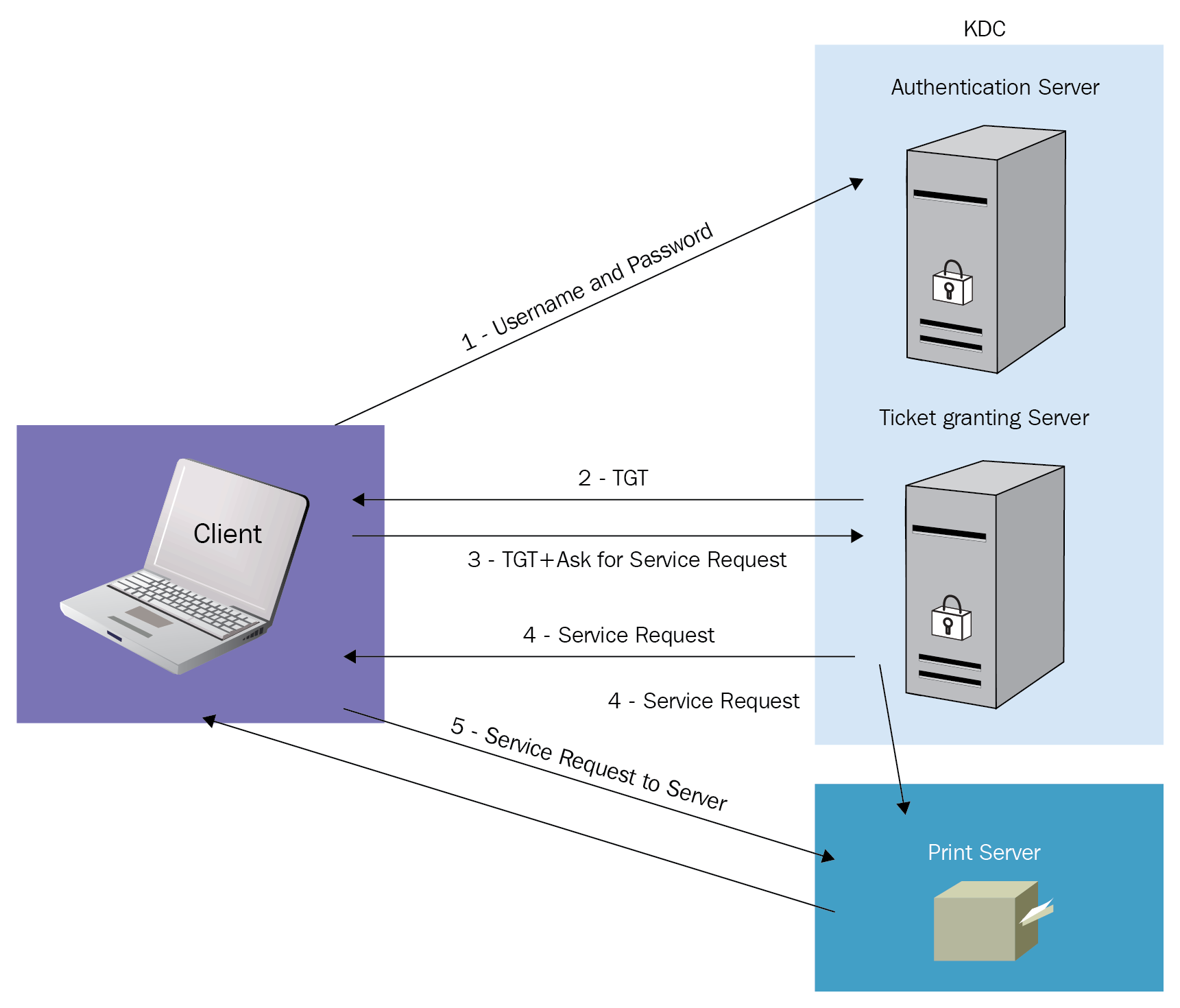
Kerberos is a cryptographic network protocol that works for authenticating users to resources, which involves a client, server, and a Key Distribution Center (KDC). Kerberos was named after Cerberus, the three-headed dog of Greek mythology, because of its three components. KDC has two components: an Authentication Server and a Ticket Granting Service, as well as the Client and the Print Server that the Client wants to access, as shown in the following diagram:
Let's try to understand...