MAC address Spoofing/ARP poisoning
The goal of any Man-in-the Middle attack is to be able to redirect traffic, not intended for you, through a device that you control. If an attacker is connected to the same wireless network as a targeted client, they can utilize various techniques to accomplish this. Kali provides many of the tools required to manipulate network services that will modify the destination of where legitimate clients are sending traffic. Once the modifications are in place, the clients will rely on the attacker's computer for doing things like name resolution or as the next hop for their IP traffic. Having this position in the network allows the attacker to spoof replies to the client or capture any traffic normally destined for the network gateway.
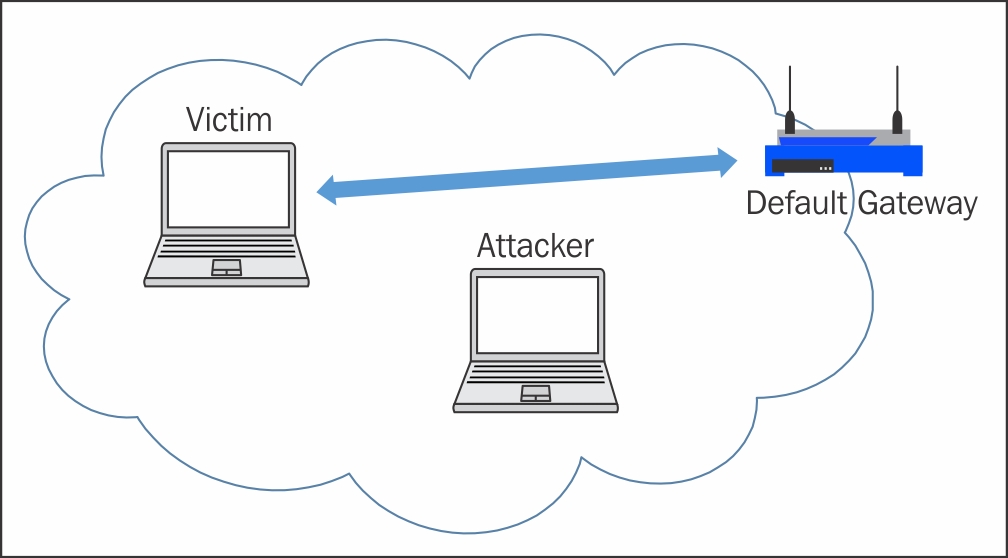
The following diagram depicts the typical state of the network where the normal communication traffic flows between the client computer and the default gateway:
On any IP-based network, wireless or otherwise, address resolution is...