Summary
You’ve now covered the threat types described on the cards from the Information Disclosure suit in the Elevation of Privilege card deck with the addition of two cards from the T.R.I.M. extension for the game. These threats detailed flaws relating to brute forcing, reconnaissance, missing cryptography both in transit and at rest, being too descriptive in messages, social engineering, file permissions, and access control.
You should now understand why sensitive data should be encrypted wherever possible, how sharing too much information (no matter how innocuous it may seem) can be harmful, and why you should always set the strongest permissions by default and then relax them as needed. Having a greater awareness of the threats in this category and having discussed how to mitigate them, be confident that you are making it as difficult as possible for your adversary to get at the data.
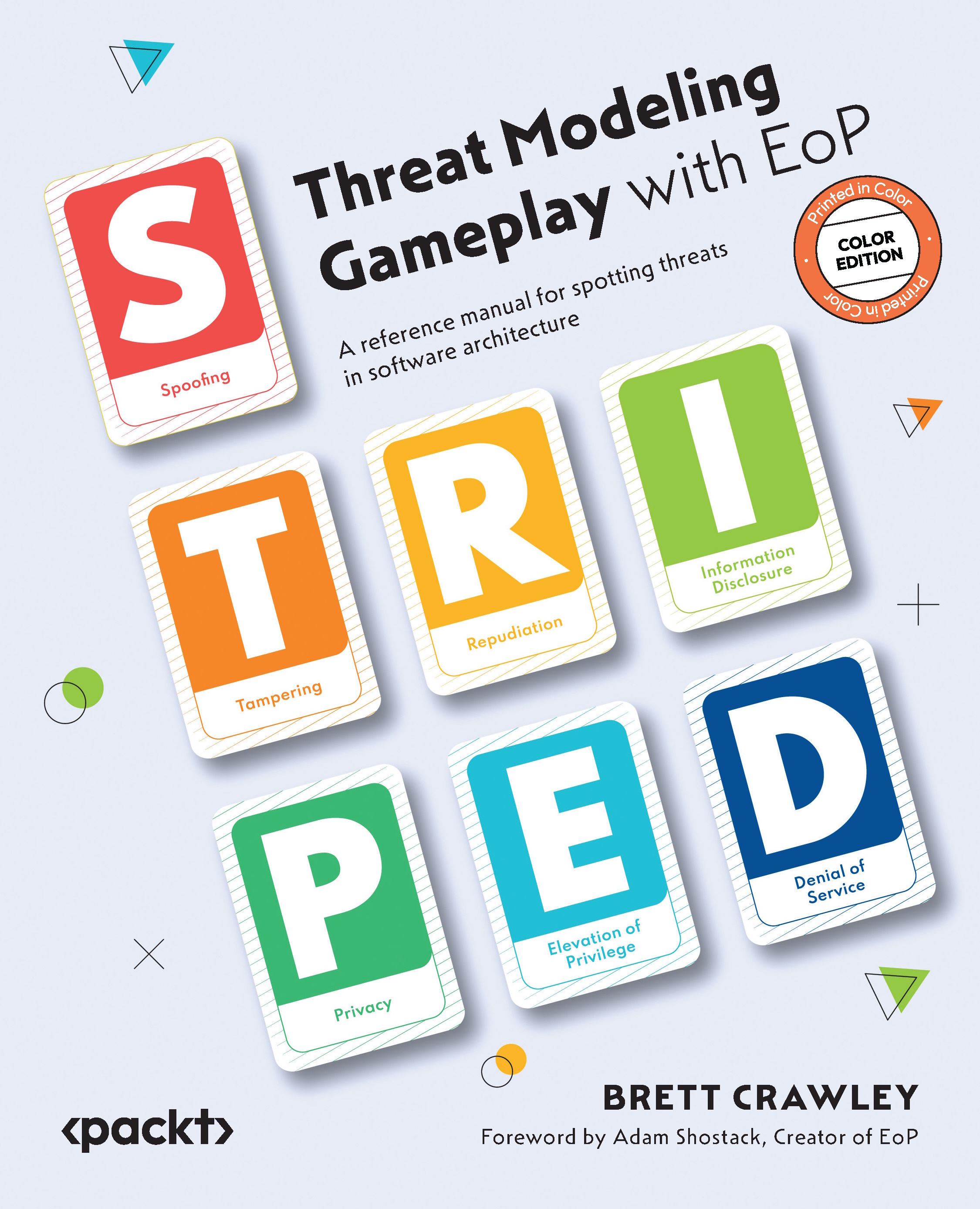
In the next chapter, we will cover the fifth S.T.R.I.D.E. category of threats or...