Reference pages
Use these pages as reference documentation when implementing the implicit grant flow in your application. Adapted from The OAuth 2.0 Authorization Framework specification [RFC 6749].
An overview of the refresh token flow
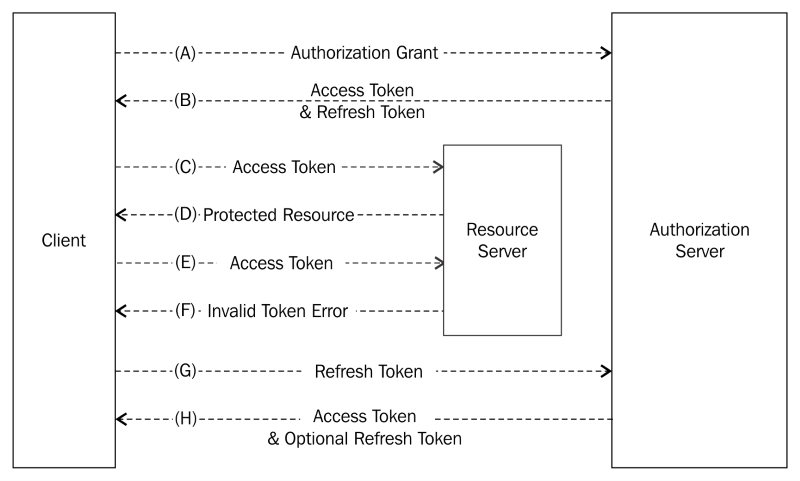
Figure 2 from RFC 6749
The steps are as follows:
A: The client requests an access token by authenticating with the service provider and presenting an authorization grant.
B: The authorization server of the service provider authenticates the client and validates the authorization grant and, if valid, issues an access token and optionally a refresh token.
C: The client makes a protected resource request to the resource server by presenting the access token.
D: The resource server validates the access token and, if valid, serves the request.
E: Steps (C) and (D) repeat until the access token expires. If the client application knows the access token has expired, or will expire shortly, it may skip to step (G). Otherwise, the client application makes another protected...























































