Configuring remote connectivity services - HTTP, TFTP, and SSH
During penetration testing and auditing, we will be required to deliver payload on target machines from our Linux. For that purpose, we will leverage basic network services such as HTTP, FTP, and SSH. Services such as and SSH are installed by default in Kali Linux but Kali does not enable any network services to minimize detection.
In this recipe, we will show you to configure and start running services securely:
Getting ready
For this recipe, you will need a to the Internet with a valid IP address.
How to do it...
Perform the following steps for this recipe:
- Let's begin with starting an Apache webserver. To start the Apache service, use the following command:
service apache2 start
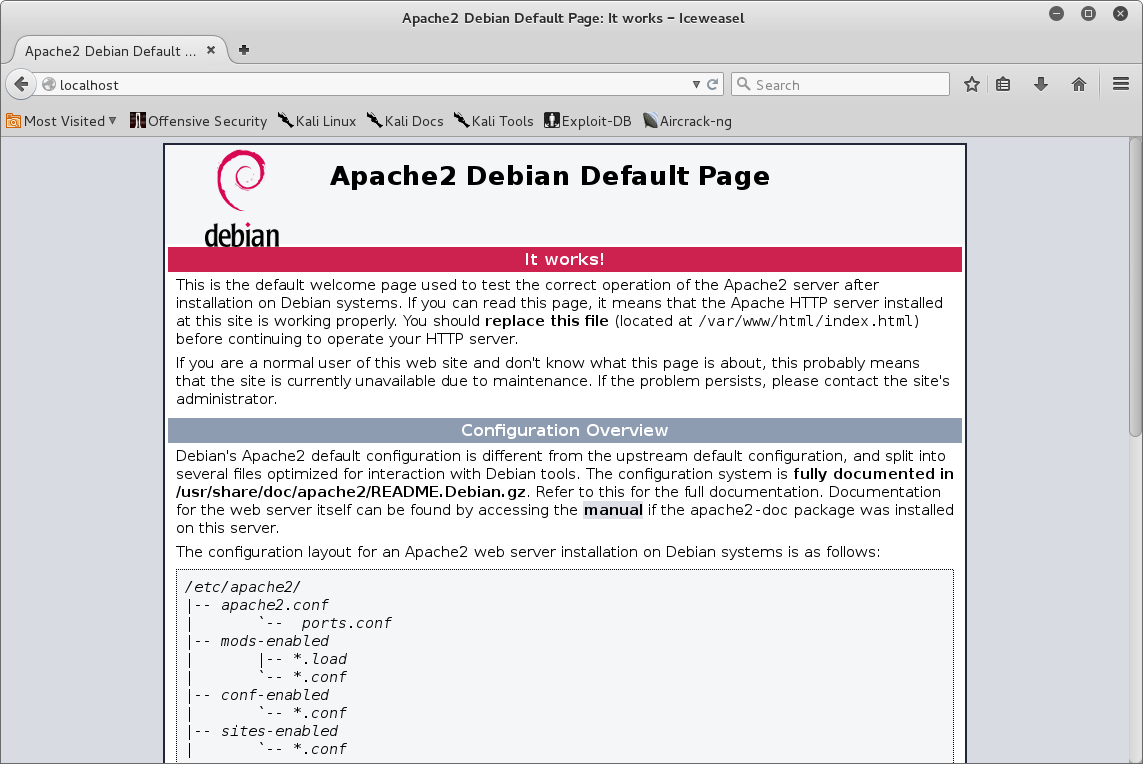
You can verify that the service is by to the localhost using a as shown in the screenshot:
- To start the SSH service, SSH keys needs to be generated. Back in Backtrack r5, you used to generate SSH keys using the
sshd-generatecommand, which is not available in Kali Linux. Using default SSH keys is a security risk and therefore a new SSH key should be generated. To generate SSH keys, you can either delete or backup your default keys generated by Kali Linux:
# cd /etc/ssh # mkdir default_kali_keys # mv ssh_host_* default_kali_keys/ # cd /root/
- First, we need remove run levels for SSH by issuing the following command:
# update-rc.d -f ssh remove
- Now we need to the SSH run by issuing the command:
# update-rc.d -f ssh defaults
- Regenerate the keys:
# dpkg-reconfigure openssh-server Creating SSH2 RSA key; this may take some time ... Creating SSH2 DSA key; this may take some time ... Creating SSH2 ECDSA key; this may take some time ... insserv: warning: current start runlevel(s) (empty) of script `ssh' overrides LSB defaults (2 3 4 5). insserv: warning: current stop runlevel(s) (2 3 4 5) of script `ssh' overrides LSB defaults (empty).
- You can check whether the SSH key hashes are different now:

- Start the SSH service using the following command:
service ssh start
- You can verify the service is using the
netstatcommand:
netstat - antp | grep ssh
- Start the FTP server using the command:
service pure-ftpd start
- To verify that the service is running, use the following command:
netstat -ant | grep ftp
- To stop any service, you can the following command:
service <servicename> stop
Here, <servicename> is the name of service required to terminate:
service ssh stop
How it works...
In this recipe, we have configured and started basic network services, which we will be using to deliver payloads to our victim machines depending on the scenario. We have started HTTP service, FTP service, and we have backed up default SSH keys and generated new SSH keys, and started the SSH service.



























































