Configuring Nessus and Metasploit
In this recipe, we will you how to install, configure, and start running Nessus and Metasploit.
Getting ready
For this recipe, we will be Nessus home feed and register for a valid license.
How to do it...
Perform the steps for this recipe:
- Open Firefox and go to
http://www.tenable.com/products/nessus/select-your-operating-system
and select the home version. On the next page, select the operating system as
6 and 7(as Kali is based on Debian Jessie) as shown in the following screenshot:

- To the Nessus, open the command in the terminal and type:
dpkg -i Nessus-6.2.0-debian6_amd64.deb
- Now, your Nessus has been installed as shown in the following screenshot:

- Once the installation is complete, start the Nessus service using the following command:
/etc/init.d/nessusd start
- Open link
https://kali:8834as shown in the screenshot:
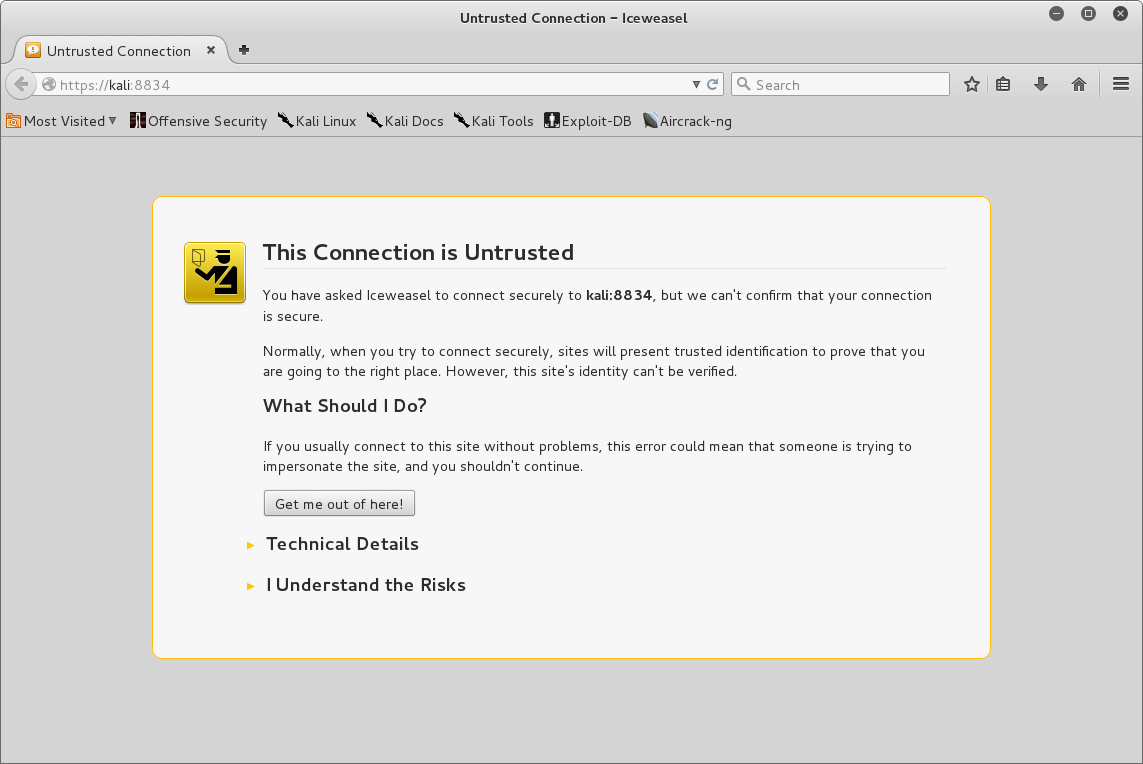
- By default, during installation, Nessus is configured for using self-signed certificates to the traffic between your browser and the Nessus server; therefore, you are seeing page shown in the preceding screenshot. If you have downloaded the Nessus from a tenable website, you can consider it safe to click on
I understand the risk and accept the certificateto continue and you will see the following page:

- Click on
Continue, and you will be shown the initial account setup page, as in following screenshot:

- Enter the username and password combination you want to create and click on
Continue. On the next page, you will be required to enter the code as shown in following screenshot:

- To obtain the activation, go to http://www.tenable.com/products/nessus-home and fill the form on the right-hand side of the page to receive the activation code. You will receive your activation code on your e-mail account. Copy the activation and enter it on this screen and continue:

Now, the Activation has been completed and Nessus will update the plugins and the tool will be ready for your use.
- We now have Nessus in place. So, let's set up Metasploit. Metasploit is installed by default during OS installation. To invoke, you will need to start the following services:
# service postgresql start [ ok ] Starting PostgreSQL 9.1 database server: main. root@Intrusion-Exploitation:~# root@Intrusion-Exploitation:~# msfconsole [ ok ] Starting Metasploit rpc server: prosvc. [ ok ] Starting Metasploit web server: thin. [ ok ] Starting Metasploit worker: worker.
- Metasploit will be started as shown in following screenshot:

How it works...
In this recipe, we have downloaded Nessus home feed and started the service. We completed the basic initial account setup and entered the account activation key to activate our home feed version of Nessus and finally updated the plugins.
Later on, we turned on PostgreSQL and Metasploit services, and finally, using msfconsole we started an instance of Metasploit.
There's more...
Nessus is a scanner and is an exploitation framework from Rapid7. However, most network environments require only vulnerability assessment and not in-depth exploitation. But, if in some cases it is needed, Metasploit is one of the best frameworks available. Similar to Nessus, Rapid7 has also launched their own vulnerability scanner called Nexpose. can be configured to be integrated with Metasploit, which allows Metasploit to use NexPose for vulnerability scanning and select exploits based on the information gathered by and thus it provides better experience as compared to using Nessus with Metasploit. For more information, visit http://www.rapid7.in/products/nexpose/ .



























































